Introduction
WebAssembly, usually called WASM, is a portable binary format that lets developers run compiled code safely across browsers, servers, edge devices, cloud platforms, and embedded environments. In simple words, it helps applications run fast, securely, and consistently without being locked to one operating system or programming language.
WebAssembly runtimes execute WASM modules, while toolchains help developers build, optimize, debug, package, and deploy those modules. In 2026+ software architecture, WASM matters because teams want lightweight workloads, safer plugin systems, faster edge execution, portable serverless functions, and better isolation than traditional scripting extensions.
Common use cases include:
- Browser-based performance-heavy apps
- Edge computing and serverless functions
- Plugin systems for SaaS platforms
- Secure sandboxing for untrusted code
- Cross-language application components
Buyers and engineering teams should evaluate:
- Runtime performance
- WASI support
- Language compatibility
- Security sandboxing
- Developer experience
- Cloud-native integration
- Observability support
- Community maturity
- Enterprise support options
- Deployment flexibility
Best for: platform engineers, backend developers, cloud-native teams, edge computing teams, DevOps teams, AI infrastructure teams, and companies building secure extension systems.
Not ideal for: teams building simple websites, small apps with no performance or portability needs, or projects where JavaScript, containers, or native binaries already solve the problem more simply.
Key Trends in WebAssembly (WASM) Runtimes & Toolchains
- WASI adoption is becoming more important as teams want WASM outside the browser for servers, edge, and cloud-native workloads.
- Edge computing is pushing WASM forward because WASM modules are lightweight, fast to start, and easier to isolate than full containers.
- AI inference at the edge is growing where small WASM modules can support lightweight model execution, pre-processing, or secure plugin logic.
- Kubernetes integration is improving as cloud-native teams explore WASM workloads beside containers.
- Security sandboxing is a major driver because WASM is useful for running third-party code with limited permissions.
- Polyglot development is expanding with Rust, C, C++, Go, AssemblyScript, .NET, and other languages targeting WASM.
- Component model maturity is improving interoperability between languages and modules.
- Developer tooling is becoming more practical with better debugging, optimization, packaging, and registry workflows.
- Serverless WASM is gaining attention because startup time and resource efficiency matter for event-driven workloads.
- Open-source ecosystems remain dominant, but enterprise support and managed services are becoming more relevant.
How We Selected These Tools
The tools below were selected using practical evaluation logic:
- Strong market mindshare among WASM developers and platform teams
- Runtime or toolchain maturity
- Relevance for browser, server, edge, or cloud-native use cases
- Language ecosystem support
- Performance and reliability signals
- Security model and sandboxing capabilities
- WASI and component model direction
- Documentation and developer onboarding quality
- Community activity and long-term ecosystem value
- Fit across solo developers, SMBs, mid-market teams, and enterprises
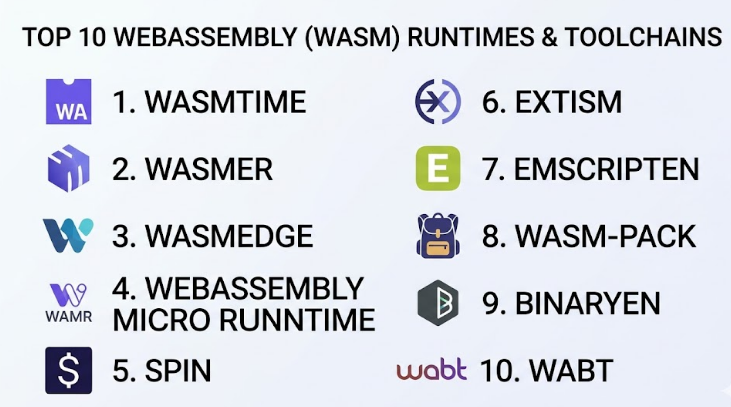
Top 10 WebAssembly (WASM) Runtimes & Toolchains
#1 — Wasmtime
Short description :
Wasmtime is a widely used WebAssembly runtime focused on WASI and secure execution outside the browser.It is popular with developers building server-side WASM, embedded runtime features, and cloud-native platforms.Wasmtime is especially strong for teams that need a standards-focused runtime with a serious security posture.It works well for Rust-heavy teams, platform engineers, and organizations experimenting with portable workloads.Its ecosystem is technical, mature, and suitable for production-minded engineering teams.
Key Features
- WASI support for server-side WebAssembly
- Strong sandboxing model
- Fast runtime execution
- Embedding support for host applications
- Rust-first ecosystem strength
- Component model direction
- CLI and API-based usage
Pros
- Strong fit for secure server-side WASM
- Good documentation and technical maturity
- Suitable for embedding WASM into applications
Cons
- May feel complex for beginners
- Enterprise support depends on use case and vendor ecosystem
- Requires WASM knowledge to use effectively
Platforms / Deployment
Linux / macOS / Windows
Self-hosted / Hybrid
Security & Compliance
Strong sandboxing and capability-based execution concepts are core to the runtime.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
Wasmtime fits well into developer and platform engineering workflows where WASM modules need to run safely inside services, CLIs, or infrastructure systems.
- Rust ecosystem
- WASI-based applications
- CLI workflows
- Embedded application runtimes
- Server-side WASM platforms
Support & Community
Wasmtime has strong documentation and a serious technical community. Enterprise support depends on how it is adopted and whether a commercial vendor is involved.
#2 — Wasmer
Short description :
Wasmer is a universal WebAssembly runtime designed to run WASM across many environments.
It is useful for teams that want portability across desktop, server, edge, and embedded scenarios.
Wasmer focuses on developer experience, packaging, and running WASM modules in flexible ways.
It is suitable for teams exploring WASM apps, plugins, and portable software distribution.
Its approach is practical for developers who want a runtime that feels approachable.
Key Features
- Cross-platform WASM runtime
- WASI support
- Package and registry ecosystem
- Multiple language embedding options
- CLI-driven workflow
- Server and edge usage support
- Developer-friendly tooling
Pros
- Good portability story
- Friendly developer experience
- Useful for experimentation and production pilots
Cons
- Some workflows may depend on ecosystem maturity
- Advanced use cases require careful architecture planning
- Enterprise compliance details may vary
Platforms / Deployment
Linux / macOS / Windows
Cloud / Self-hosted / Hybrid
Security & Compliance
WASM sandboxing is part of the runtime model.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
Wasmer integrates with development pipelines where teams need to package, run, and distribute WASM modules across environments.
- CLI tooling
- WASI modules
- Language embeddings
- Package workflows
- Server-side WASM projects
Support & Community
Wasmer has active documentation and community resources. Support options may vary depending on edition, deployment model, and commercial requirements.
#3 — WasmEdge
Short description :
WasmEdge is a lightweight WebAssembly runtime often used for cloud-native, edge, serverless, and embedded workloads.
It is recognized in the cloud-native ecosystem and is attractive for teams building fast, portable functions.
WasmEdge is useful when startup time, small footprint, and secure execution are important.
It can support microservices, IoT, edge functions, and decentralized application patterns.
It is a good fit for platform teams evaluating WASM alongside containers.
Key Features
- Lightweight runtime architecture
- Edge and cloud-native focus
- WASI support
- Serverless function use cases
- Plugin-style execution
- Support for multiple language workflows
- Performance-focused runtime design
Pros
- Strong fit for edge and cloud-native workloads
- Lightweight compared with many traditional runtime models
- Good for serverless experimentation
Cons
- Requires WASM and platform engineering skills
- Ecosystem choices may need validation
- Not every workload benefits from WASM deployment
Platforms / Deployment
Linux / macOS / Windows
Cloud / Self-hosted / Hybrid
Security & Compliance
Sandboxing is part of the WebAssembly execution model.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
WasmEdge fits well into cloud-native, edge, and serverless environments where small, fast, isolated workloads are useful.
- Kubernetes-adjacent workflows
- Edge platforms
- Serverless functions
- IoT scenarios
- Microservice extensions
Support & Community
WasmEdge has strong open-source visibility and cloud-native community relevance. Enterprise support details vary by deployment and vendor relationship.
#4 — WebAssembly Micro Runtime
Short description :
WebAssembly Micro Runtime, often called WAMR, is a compact runtime designed for embedded, IoT, and resource-constrained environments.
It is useful when teams need WASM execution on devices where full runtime overhead is not acceptable.
WAMR supports lightweight execution and is practical for systems programming use cases.
It fits teams working with edge devices, embedded platforms, and secure application isolation.
Its main value is small footprint and runtime flexibility.
Key Features
- Lightweight runtime footprint
- Embedded and IoT suitability
- Interpreter and compilation options
- WASI-related support
- Host embedding capabilities
- Resource-constrained execution
- Portable runtime design
Pros
- Strong fit for embedded use cases
- Lightweight compared with broader runtimes
- Useful for constrained environments
Cons
- Less beginner-friendly than browser-focused tools
- Use cases are more specialized
- Documentation depth may vary by scenario
Platforms / Deployment
Linux / macOS / Windows / Embedded systems
Self-hosted / Hybrid
Security & Compliance
Sandboxing is part of the WASM model, but compliance certifications are Not publicly stated.
Integrations & Ecosystem
WAMR is best used where WASM needs to be embedded inside devices, gateways, agents, or constrained systems.
- Embedded systems
- IoT runtimes
- Edge agents
- Native host applications
- C/C++ workflows
Support & Community
Community strength is meaningful in embedded and systems circles. Support and onboarding may require experienced engineering teams.
#5 — Spin
Short description :
Spin is a developer framework for building and running WebAssembly applications, especially serverless-style apps.It helps developers package WASM components into application workflows without manually handling every runtime detail.Spin is useful for teams building HTTP services, event-driven functions, and lightweight distributed apps.It is more application-focused than low-level runtimes.It works well for developers who want a practical path into server-side WASM.
Key Features
- Serverless-style WASM application framework
- HTTP and event-driven workload support
- Developer-friendly project structure
- Local development workflow
- Component-based application model
- Cloud and self-hosted deployment options
- Good fit for microservice-style apps
Pros
- Easier entry point for app developers
- Strong fit for serverless WASM
- Helps structure real applications
Cons
- Less low-level control than raw runtimes
- Best value depends on platform adoption
- Not needed for simple WASM experiments
Platforms / Deployment
Linux / macOS / Windows
Cloud / Self-hosted / Hybrid
Security & Compliance
Security depends on runtime, deployment, and platform configuration.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
Spin connects WASM development with application deployment patterns, especially for web services and event-driven workloads.
- HTTP services
- Serverless-style functions
- Component workflows
- Local developer tools
- Cloud-native environments
Support & Community
Spin has growing documentation and developer community support. Commercial support depends on the platform and vendor model used.
#6 — Extism
Short description :
Extism is a framework for building plugin systems using WebAssembly.
It is useful for SaaS platforms, developer tools, automation systems, and applications that need safe third-party extensions.Instead of using WASM only as an app runtime, Extism focuses on embeddable plugins.
It helps teams add extension points without giving plugins unsafe system access.
This makes it valuable for companies building customizable software platforms.
Key Features
- WASM-based plugin framework
- Multi-language SDK support
- Secure extension model
- Host application embedding
- Plugin portability
- Developer-friendly APIs
- Useful for SaaS extensibility
Pros
- Strong fit for plugin architectures
- Reduces risk from untrusted extensions
- Supports multi-language teams
Cons
- Not a general-purpose runtime replacement
- Requires thoughtful host API design
- Best suited for plugin-first use cases
Platforms / Deployment
Linux / macOS / Windows
Self-hosted / Hybrid
Security & Compliance
WASM sandboxing helps isolate plugins.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
Extism integrates with applications that need controlled plugin execution and cross-language extension support.
- Host application SDKs
- Plugin APIs
- SaaS platforms
- Developer tooling
- Automation engines
Support & Community
Extism has useful documentation for plugin use cases. Community strength is growing, especially among teams building extensible software.
#7 — Emscripten
Short description :
Emscripten is a mature compiler toolchain for compiling C and C++ code to WebAssembly.
It is widely used for porting existing native applications, games, libraries, and performance-heavy code to the web.Emscripten is especially strong when teams need browser compatibility and access to web APIs.
It helps bring complex native codebases into browser or WASM runtime environments.
It is best for teams with C/C++ experience and performance-oriented workloads.
Key Features
- C/C++ to WebAssembly compilation
- LLVM-based workflow
- Browser-focused output
- Web API support
- SDL, OpenGL/WebGL-related workflows
- Optimization options
- Mature porting ecosystem
Pros
- Excellent for porting native code
- Mature and widely used
- Strong browser-focused capabilities
Cons
- Can be complex for beginners
- Build output may need optimization
- Best suited to C/C++ style projects
Platforms / Deployment
Linux / macOS / Windows
Web / Self-hosted / Hybrid
Security & Compliance
Security depends on application code, browser sandboxing, and deployment environment.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
Emscripten fits into build pipelines where existing native code needs to be compiled for web or WASM execution.
- C/C++ projects
- LLVM workflows
- Browser applications
- Game engines
- Graphics-heavy applications
Support & Community
Emscripten has strong documentation, long-term community adoption, and many examples. Support is largely community and ecosystem-driven.
#8 — wasm-pack
Short description :
wasm-pack is a toolchain for building and packaging Rust-generated WebAssembly.
It is commonly used by Rust developers who want to publish WASM packages for JavaScript and web projects.The tool helps simplify build, test, and packaging steps around Rust-to-WASM workflows.
It is valuable for teams that want strong type safety and Rust performance in browser or package ecosystems.
It is not a runtime but an important toolchain in WASM development.
Key Features
- Rust-to-WASM build workflow
- JavaScript package integration
- Testing support
- Packaging automation
- npm-style publishing workflow
- wasm-bindgen ecosystem support
- Developer-friendly CLI
Pros
- Excellent for Rust WASM projects
- Simplifies packaging and publishing
- Good fit for frontend and library teams
Cons
- Rust-focused only
- Not a standalone runtime
- Requires knowledge of Rust and WASM bindings
Platforms / Deployment
Linux / macOS / Windows
Web / Self-hosted / Hybrid
Security & Compliance
Security depends on package workflow, dependency management, and deployment environment.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
wasm-pack is tightly aligned with Rust, JavaScript packaging, and browser-based WASM development.
- Rust projects
- wasm-bindgen
- JavaScript packages
- Browser apps
- CI/CD build pipelines
Support & Community
wasm-pack has strong Rust community relevance. Documentation is useful, but best results require Rust and frontend build knowledge.
#9 — Binaryen
Short description :
Binaryen is a compiler and optimization toolkit for WebAssembly.
It is used to optimize, transform, and analyze WASM code during build workflows.
Binaryen is especially useful for compiler authors, toolchain builders, and teams optimizing WASM output size and performance.It is not an application runtime but plays a major role in serious WASM build pipelines.
It is best for advanced engineering teams working deeply with WASM output.
Key Features
- WASM optimization tools
- Compiler infrastructure
- Code transformation support
- wasm-opt utility
- Toolchain integration
- Size and performance optimization
- Useful for advanced build systems
Pros
- Strong optimization capabilities
- Useful for compiler and tooling teams
- Helps improve WASM output quality
Cons
- Not beginner-friendly
- Not a runtime or app framework
- Best for advanced use cases
Platforms / Deployment
Linux / macOS / Windows
Self-hosted / Hybrid
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Binaryen is usually part of build and compiler workflows rather than runtime deployment.
- Compiler toolchains
- Build pipelines
- Emscripten-related workflows
- WASM optimization steps
- Custom tooling
Support & Community
Binaryen has strong relevance in the WASM compiler ecosystem. Support is mainly documentation and open-source community driven.
#10 — WABT
Short description :
WABT, the WebAssembly Binary Toolkit, is a collection of tools for working directly with WASM binaries and text format.It is useful for inspection, conversion, debugging, testing, and learning how WebAssembly works internally.Developers use it to convert between binary WASM and readable text format.
It is best for low-level debugging, education, and toolchain validation.
It is not a production runtime but remains important in the WASM tooling ecosystem.
Key Features
- wasm2wat conversion
- wat2wasm conversion
- WASM inspection utilities
- Validation tools
- Debugging support
- Low-level binary understanding
- Useful for testing and education
Pros
- Excellent for inspecting WASM modules
- Helpful for debugging and learning
- Lightweight and focused
Cons
- Not an application framework
- Not a runtime
- Mainly useful for technical users
Platforms / Deployment
Linux / macOS / Windows
Self-hosted / Hybrid
Security & Compliance
Not publicly stated
Integrations & Ecosystem
WABT is commonly used in developer tooling, testing, and low-level WASM inspection workflows.
- WASM debugging
- Binary inspection
- Compiler testing
- Educational workflows
- CI validation tasks
Support & Community
WABT has strong recognition among WASM developers. Support is mainly community-based with practical documentation.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment (Cloud/Self-hosted/Hybrid) | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Wasmtime | Secure server-side WASM | Linux, macOS, Windows | Self-hosted / Hybrid | Standards-focused WASI runtime | N/A |
| Wasmer | Portable WASM execution | Linux, macOS, Windows | Cloud / Self-hosted / Hybrid | Universal runtime and packaging ecosystem | N/A |
| WasmEdge | Edge and cloud-native workloads | Linux, macOS, Windows | Cloud / Self-hosted / Hybrid | Lightweight edge-focused runtime | N/A |
| WebAssembly Micro Runtime | Embedded and IoT systems | Linux, macOS, Windows, Embedded | Self-hosted / Hybrid | Small-footprint runtime | N/A |
| Spin | Serverless WASM applications | Linux, macOS, Windows | Cloud / Self-hosted / Hybrid | App framework for WASM services | N/A |
| Extism | Plugin systems | Linux, macOS, Windows | Self-hosted / Hybrid | WASM-based plugin framework | N/A |
| Emscripten | C/C++ to WASM compilation | Linux, macOS, Windows | Web / Self-hosted / Hybrid | Mature native-code porting toolchain | N/A |
| wasm-pack | Rust WASM packaging | Linux, macOS, Windows | Web / Self-hosted / Hybrid | Rust-to-WASM package workflow | N/A |
| Binaryen | WASM optimization | Linux, macOS, Windows | Self-hosted / Hybrid | wasm-opt and compiler tooling | N/A |
| WABT | WASM inspection and conversion | Linux, macOS, Windows | Self-hosted / Hybrid | Binary/text toolkit for WASM | N/A |
Evaluation & WebAssembly (WASM) Runtimes & Toolchains
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Wasmtime | 9 | 7 | 8 | 9 | 9 | 8 | 8 | 8.25 |
| Wasmer | 8 | 8 | 8 | 8 | 8 | 8 | 8 | 8.00 |
| WasmEdge | 8 | 7 | 8 | 8 | 9 | 8 | 8 | 8.00 |
| WebAssembly Micro Runtime | 8 | 6 | 7 | 8 | 8 | 7 | 8 | 7.45 |
| Spin | 8 | 8 | 8 | 7 | 8 | 8 | 8 | 7.90 |
| Extism | 8 | 8 | 8 | 8 | 7 | 7 | 8 | 7.75 |
| Emscripten | 9 | 6 | 8 | 7 | 8 | 8 | 9 | 8.00 |
| wasm-pack | 7 | 8 | 8 | 7 | 7 | 7 | 8 | 7.45 |
| Binaryen | 8 | 5 | 7 | 6 | 8 | 7 | 8 | 7.10 |
| WABT | 7 | 6 | 6 | 6 | 7 | 7 | 8 | 6.80 |
These scores are comparative, not absolute. A higher score does not mean the tool is best for every team. For example, WABT scores lower as a full platform, but it is still excellent for inspection and debugging. Wasmtime, Wasmer, and WasmEdge score strongly because they cover runtime needs more broadly. Toolchains such as Emscripten, wasm-pack, Binaryen, and WABT should be judged by build and optimization value rather than runtime coverage.
Which WebAssembly (WASM) Runtimes & Toolchains
Solo / Freelancer
Solo developers should start with tools that reduce setup time. For Rust-based projects, wasm-pack is a practical choice. For C/C++ browser projects, Emscripten is usually more suitable. If the goal is to run WASM outside the browser, Wasmtime or Wasmer are good starting points.
SMB
SMBs should choose tools based on business use case. If the team is building plugins, Extism is attractive. If they are building lightweight server-side WASM apps, Spin can reduce complexity. For general runtime experimentation, Wasmer gives a friendly entry point.
Mid-Market
Mid-market teams need stronger governance, repeatable deployment, and integration with CI/CD. Wasmtime, WasmEdge, and Spin are strong options depending on whether the workload is runtime-focused, edge-focused, or application-focused. Teams should validate observability, security boundaries, and build automation before production use.
Enterprise
Enterprises should prioritize security, lifecycle management, runtime isolation, support options, and platform integration. Wasmtime is strong for standards-focused secure execution. WasmEdge is practical for edge and cloud-native pilots. Extism can be useful for controlled enterprise plugin ecosystems.
Budget vs Premium
Most WASM tools are open-source or developer-first, but the real cost is engineering time. A “free” runtime may still require skilled platform engineers, security reviews, CI/CD integration, and observability setup. Teams with limited budgets should start with a narrow pilot instead of attempting a large platform migration.
Feature Depth vs Ease of Use
For deep runtime control, choose Wasmtime, Wasmer, or WasmEdge. For easier application development, consider Spin. For plugin systems, Extism is more direct. For build workflows, Emscripten, wasm-pack, Binaryen, and WABT are specialized and should be used as part of the toolchain.
Integrations & Scalability-
Scalability depends on how WASM is deployed. Runtime selection should match the target environment: browser, server, edge, embedded, Kubernetes, or application plugin system. Teams should validate CI/CD, registry workflows, logs, metrics, and rollback strategy before scaling.
Security & Compliance Needs
For security-sensitive use cases, focus on sandboxing, host permissions, module signing, dependency scanning, auditability, and least-privilege execution. Do not assume that WASM automatically solves compliance. Compliance depends on the full platform, deployment model, data handling, and operational controls.
Frequently Asked Questions (FAQs)
1. What is the difference between a WASM runtime and a WASM toolchain?
A runtime executes WebAssembly modules. A toolchain helps build, compile, optimize, inspect, or package those modules. For example, Wasmtime is a runtime, while Emscripten and Binaryen are toolchain-focused.
2. Is WebAssembly only for browsers?
No. WASM started with strong browser use cases, but modern WASM is also used in servers, edge platforms, embedded systems, plugin architectures, and cloud-native environments.
3. Which WASM runtime is best for server-side workloads?
Wasmtime, Wasmer, and WasmEdge are common choices for server-side WASM. The best choice depends on WASI needs, embedding requirements, performance expectations, and ecosystem fit.
4. Is WebAssembly more secure than containers?
WASM can provide strong sandboxing, but it is not a complete replacement for containers in every case. Security depends on runtime configuration, host permissions, supply chain controls, and deployment architecture.
5. What pricing model should buyers expect?
Many tools in this category are open-source. However, commercial support, managed platforms, enterprise hosting, security reviews, and engineering implementation may create additional costs.
6. How long does onboarding usually take?
A small proof of concept can be started quickly by experienced developers. Production adoption takes longer because teams must validate build pipelines, runtime behavior, security controls, observability, and deployment patterns.
7. What are common mistakes when adopting WASM?
Common mistakes include choosing WASM only for hype, ignoring operational tooling, assuming all languages have equal support, skipping security reviews, and not testing performance against real workloads.
8. Can WASM replace Docker or Kubernetes?
Not fully for most teams. WASM can complement containers and Kubernetes for lightweight workloads, edge functions, and secure plugins. Containers remain better for many full application deployment scenarios.
9. Which languages work well with WebAssembly?
Rust, C, and C++ are among the strongest choices. Other languages can target WASM too, but maturity, runtime size, bindings, and ecosystem quality vary.
10. How should teams evaluate WASM integrations?
Teams should check CI/CD support, language bindings, WASI compatibility, registry workflows, observability, host APIs, deployment targets, and how the runtime fits existing infrastructure.
Conclusion
WebAssembly runtimes and toolchains are becoming important building blocks for modern software teams that need portability, security, fast startup, and flexible deployment across browser, server, edge, and embedded environments. However, there is no single best tool for every use case. Wasmtime is strong for secure server-side execution, Wasmer is useful for portability, WasmEdge fits edge and cloud-native scenarios, Spin helps with serverless WASM apps, and Extism is practical for plugin systems. Toolchains like Emscripten, wasm-pack, Binaryen, and WABT are essential when building, optimizing, and inspecting WASM modules.