Introduction
eBPF Observability & Runtime Security Tools help teams see what is happening inside Linux systems, Kubernetes clusters, containers, networks, and applications with very low overhead. eBPF allows security and platform teams to collect deep runtime signals directly from the kernel without changing application code.
These tools matter because modern systems are distributed, containerized, and fast-moving. Traditional monitoring often misses short-lived containers, hidden network paths, suspicious runtime behavior, and kernel-level activity. eBPF tools help detect performance issues, service communication problems, policy violations, abnormal process behavior, and runtime attacks.
Common use cases include Kubernetes visibility, container runtime security, network troubleshooting, API dependency mapping, threat detection, zero-trust enforcement, and cloud workload monitoring.
Buyers should evaluate:
- Kubernetes and container visibility
- Runtime threat detection
- Network flow analysis
- Performance overhead
- Policy enforcement
- Cloud and hybrid support
- SIEM and DevOps integrations
- Ease of deployment
- Alert quality
- Support and documentation
Best for: DevOps teams, SRE teams, platform engineers, cloud security teams, Kubernetes administrators, SOC teams, and enterprises running containerized or cloud-native workloads.
Not ideal for: Small teams running simple static websites, non-Linux-heavy environments, or companies that only need basic uptime monitoring.
Key Trends in eBPF Observability & Runtime Security Tools
- Kubernetes-native observability is becoming a major use case, especially for service maps, pod-to-pod traffic, and container behavior.
- Runtime security is moving closer to the kernel, allowing teams to detect suspicious activity before damage spreads.
- AI-assisted alert analysis is growing, helping teams reduce noise and prioritize real incidents.
- Network visibility is becoming deeper, with tools showing DNS, HTTP, TCP, service identity, and workload-level traffic.
- Cloud-native security platforms are adding eBPF agents to improve workload monitoring.
- Low-overhead monitoring is now a major buyer requirement, especially for high-scale production systems.
- Policy-as-code is becoming more common for runtime controls and network enforcement.
- Developer-friendly debugging is improving, helping engineering teams troubleshoot production systems faster.
- Open-source eBPF projects continue to shape the market, especially for Kubernetes networking and runtime visibility.
- Security and observability are converging, with one platform often handling both performance and threat detection.
How We Selected These Tools
The tools were selected using practical SaaS and enterprise security evaluation logic:
- Strong relevance to eBPF-based observability or runtime security
- Market recognition among cloud-native, Kubernetes, DevOps, or security teams
- Support for container, Kubernetes, and Linux workload environments
- Depth of runtime visibility and threat detection
- Integration with modern cloud and DevSecOps workflows
- Reliability and scalability signals for production use
- Fit across SMB, mid-market, and enterprise teams
- Strength of documentation, support, and ecosystem
- Balance between open-source and commercial platforms
- Practical usefulness for real-world operations and security teams
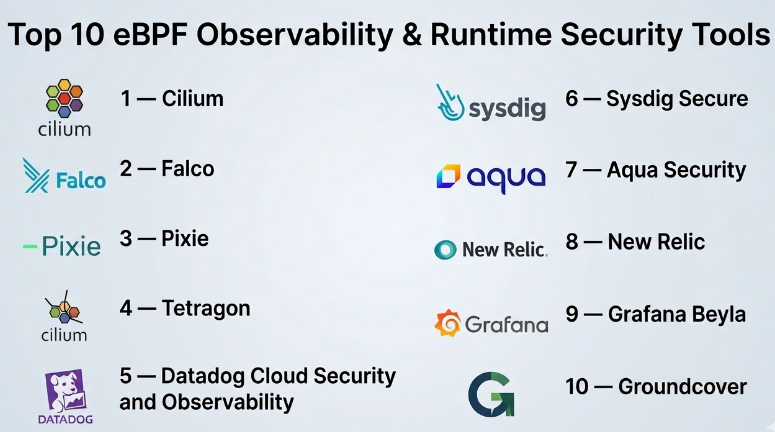
Top 10 eBPF Observability & Runtime Security Tools
#1 — Cilium
Short description :
Cilium is a popular eBPF-based networking, observability, and security platform for Kubernetes and cloud-native environments. It helps teams manage service connectivity, network policy, load balancing, and runtime visibility. Cilium is widely used by platform engineering teams that need scalable Kubernetes networking. It is especially strong where observability and network security must work together. It is best for organizations building modern Kubernetes platforms.
Key Features
- eBPF-powered Kubernetes networking
- Network policy enforcement
- Service mesh capabilities
- Runtime visibility with Hubble
- Load balancing support
- Identity-aware security controls
- Strong cloud-native ecosystem
Pros
- Excellent Kubernetes networking and visibility
- Strong open-source adoption
- Good fit for platform engineering teams
Cons
- Can be complex for beginners
- Requires Kubernetes and networking knowledge
- Advanced setup may need skilled operators
Platforms / Deployment
Linux / Kubernetes / Cloud / Self-hosted / Hybrid
Security & Compliance
RBAC and policy controls are commonly supported in Kubernetes-based deployments.
SOC 2, ISO 27001, HIPAA: Not publicly stated.
Integrations & Ecosystem
Cilium integrates well with cloud-native infrastructure and Kubernetes operations.
- Kubernetes
- Prometheus
- Grafana
- Hubble
- Cloud platforms
- CI/CD workflows
Support & Community
Cilium has strong documentation and a large open-source community. Commercial support is available through enterprise offerings.
#2 — Falco
Short description :
Falco is an open-source runtime security tool designed to detect suspicious behavior in Linux and Kubernetes environments. It uses system call activity and runtime rules to identify threats such as shell access, privilege escalation, file changes, and abnormal process behavior. Falco is widely used by cloud-native security teams. It is best for organizations that want rule-based runtime detection. It works well as part of a DevSecOps security stack.
Key Features
- Runtime threat detection
- System call monitoring
- Kubernetes-aware security rules
- Custom rule creation
- Alerting integrations
- Container behavior detection
- Open-source ecosystem
Pros
- Strong runtime security focus
- Flexible custom rules
- Good community support
Cons
- Rule tuning can take time
- May create noisy alerts if not configured well
- Requires Linux and Kubernetes knowledge
Platforms / Deployment
Linux / Kubernetes / Containers / Cloud / Self-hosted / Hybrid
Security & Compliance
Not publicly stated.
Integrations & Ecosystem
Falco works well with security monitoring and incident response workflows.
- Kubernetes
- Prometheus
- Grafana
- SIEM platforms
- Slack or webhook alerts
- Cloud-native security stacks
Support & Community
Falco has strong open-source community support, active documentation, and commercial ecosystem support through vendors.
#3 — Pixie
Short description :
Pixie is an eBPF-based observability tool for Kubernetes applications. It automatically collects telemetry from applications without requiring code changes or manual instrumentation. Pixie is useful for debugging services, tracing requests, inspecting network traffic, and understanding application behavior. It is best for developers, SREs, and platform teams working in Kubernetes. It helps reduce the effort needed for production troubleshooting.
Key Features
- Auto-telemetry using eBPF
- Kubernetes service visibility
- Request tracing
- Network traffic inspection
- Application performance debugging
- No manual instrumentation required
- Developer-friendly dashboards
Pros
- Fast Kubernetes troubleshooting
- Low manual setup compared with traditional tracing
- Useful for developers and SREs
Cons
- Kubernetes-focused use case
- May not replace full enterprise APM
- Advanced customization may require learning
Platforms / Deployment
Linux / Kubernetes / Cloud / Self-hosted / Hybrid
Security & Compliance
Not publicly stated.
Integrations & Ecosystem
Pixie is designed for Kubernetes observability and developer workflows.
- Kubernetes
- Prometheus
- Grafana
- OpenTelemetry workflows
- Cloud-native monitoring
- Developer debugging tools
Support & Community
Pixie has open-source documentation and community support. Commercial support may vary based on deployment and vendor ecosystem.
#4 — Tetragon
Short description :
Tetragon is an eBPF-based runtime security and observability tool focused on Kubernetes and Linux workloads. It helps teams monitor process execution, network activity, file access, and security-relevant events. Tetragon is useful for detecting runtime attacks, enforcing policies, and understanding workload behavior. It is suitable for platform and security teams that already work with cloud-native systems. It is best for deep runtime visibility.
Key Features
- Runtime security visibility
- Process execution monitoring
- Network event tracking
- File access monitoring
- Kubernetes-aware events
- Policy enforcement capabilities
- eBPF-based telemetry
Pros
- Strong runtime behavior visibility
- Good fit with Kubernetes security workflows
- Useful for incident investigation
Cons
- Requires security tuning
- Best suited for technical teams
- May need integration work for full SOC workflows
Platforms / Deployment
Linux / Kubernetes / Cloud / Self-hosted / Hybrid
Security & Compliance
Not publicly stated.
Integrations & Ecosystem
Tetragon fits well into Kubernetes and cloud-native security environments.
- Kubernetes
- Cilium ecosystem
- SIEM tools
- Security dashboards
- Policy workflows
- DevSecOps pipelines
Support & Community
Tetragon has open-source documentation and community support. Enterprise support may depend on vendor packaging.
#5 — Datadog Cloud Security and Observability
Short description :
Datadog provides broad observability and cloud security capabilities, including workload monitoring, runtime signals, infrastructure visibility, and container insights. It is suitable for teams that want a unified platform for metrics, logs, traces, security alerts, and cloud monitoring. eBPF-powered telemetry supports deeper visibility in modern workloads. Datadog is best for mid-market and enterprise teams that want one commercial platform. It is especially useful where observability and security need shared context.
Key Features
- Infrastructure monitoring
- Container and Kubernetes visibility
- Runtime security monitoring
- Cloud workload insights
- APM, logs, and metrics
- Alerting and dashboards
- Large integration ecosystem
Pros
- Broad observability platform
- Strong integration ecosystem
- Useful for teams wanting unified monitoring
Cons
- Cost can increase at scale
- Feature depth may require careful setup
- Not fully open-source
Platforms / Deployment
Web / Linux / Windows / macOS / Cloud / Hybrid
Security & Compliance
SSO, RBAC, audit logs, and enterprise security controls are commonly available.
SOC 2, ISO 27001, GDPR: Generally associated with enterprise SaaS security programs, but buyers should validate based on plan and region.
Integrations & Ecosystem
Datadog has one of the broadest observability integration ecosystems.
- Kubernetes
- Docker
- AWS, Azure, Google Cloud
- CI/CD platforms
- SIEM workflows
- Incident management tools
Support & Community
Datadog provides strong documentation, support tiers, onboarding resources, and a large user ecosystem.
#6 — Sysdig Secure
Short description :
Sysdig Secure is a cloud-native security platform with strong runtime security, Kubernetes security, and container monitoring capabilities. It uses deep runtime visibility to detect suspicious behavior and support compliance workflows. Sysdig is useful for organizations running containers and Kubernetes at scale. It helps security and DevOps teams detect threats, prioritize risks, and investigate incidents. It is best for teams that need runtime security plus cloud-native context.
Key Features
- Runtime threat detection
- Kubernetes security posture
- Container security monitoring
- Vulnerability prioritization
- Compliance reporting
- eBPF-based visibility
- Cloud security integrations
Pros
- Strong cloud-native security focus
- Good runtime detection capabilities
- Useful for Kubernetes-heavy teams
Cons
- Can require tuning and onboarding
- May be more than needed for small teams
- Pricing can vary by scale
Platforms / Deployment
Linux / Kubernetes / Cloud / Hybrid
Security & Compliance
Enterprise security controls are commonly available. Specific certification details should be validated by buyers.
SOC 2, ISO 27001, HIPAA: Not publicly stated.
Integrations & Ecosystem
Sysdig fits into DevSecOps and cloud security workflows.
- Kubernetes
- Container registries
- Cloud platforms
- CI/CD tools
- SIEM tools
- Incident response workflows
Support & Community
Sysdig provides documentation, commercial support, onboarding options, and a strong cloud-native security community.
#7 — Aqua Security
Short description :
Aqua Security provides cloud-native application protection with capabilities across container security, Kubernetes security, runtime protection, vulnerability management, and compliance. It is suitable for enterprises that want security from build to runtime. eBPF-based runtime controls can help detect and block suspicious workload behavior. Aqua is best for organizations that need a full cloud-native security platform. It is especially useful for regulated and enterprise Kubernetes environments.
Key Features
- Container runtime protection
- Kubernetes security controls
- Vulnerability management
- Cloud workload protection
- Policy enforcement
- Compliance reporting
- DevSecOps workflow support
Pros
- Broad cloud-native security coverage
- Strong runtime protection focus
- Good fit for enterprise security teams
Cons
- May be complex for small teams
- Requires careful policy tuning
- Broad platform may need phased rollout
Platforms / Deployment
Linux / Kubernetes / Cloud / Self-hosted / Hybrid
Security & Compliance
Enterprise controls such as RBAC, audit logs, and policy enforcement are commonly expected.
SOC 2, ISO 27001, HIPAA: Not publicly stated.
Integrations & Ecosystem
Aqua integrates across build, deploy, and runtime security workflows.
- Kubernetes
- Container registries
- CI/CD pipelines
- Cloud platforms
- SIEM systems
- Ticketing and security tools
Support & Community
Aqua provides enterprise support, documentation, training resources, and onboarding options.
#8 — New Relic
Short description :
New Relic is an observability platform used for application performance monitoring, infrastructure monitoring, logs, traces, and Kubernetes visibility. It supports modern cloud-native observability needs and can help teams understand application and infrastructure behavior. eBPF-related visibility can improve low-level system and workload insights. New Relic is best for teams that want strong developer-friendly observability. It is useful for SRE, DevOps, and engineering teams managing production applications.
Key Features
- APM and infrastructure monitoring
- Kubernetes observability
- Logs, metrics, and traces
- Service maps
- Alerting and dashboards
- Developer-friendly workflows
- Broad integration options
Pros
- Strong full-stack observability
- Good developer experience
- Useful for troubleshooting production systems
Cons
- Runtime security is not its main focus
- Cost can grow with usage
- Advanced setup may require observability maturity
Platforms / Deployment
Web / Linux / Windows / macOS / Cloud / Hybrid
Security & Compliance
SSO, RBAC, and audit controls are commonly available in enterprise plans. Specific compliance details should be validated.
SOC 2, ISO 27001, HIPAA: Not publicly stated.
Integrations & Ecosystem
New Relic works well in application and infrastructure observability ecosystems.
- Kubernetes
- Cloud platforms
- CI/CD tools
- OpenTelemetry
- Incident management tools
- Log and metric pipelines
Support & Community
New Relic offers documentation, support options, onboarding material, and a large user community.
#9 — Grafana Beyla
Short description :
Grafana Beyla is an eBPF-based auto-instrumentation tool that helps collect application observability signals without changing code. It is especially useful for teams using Prometheus, Grafana, and OpenTelemetry-based monitoring. Beyla can help collect service-level telemetry such as HTTP and network activity. It is best for engineering teams that want lightweight observability for cloud-native applications. It fits well into open-source observability stacks.
Key Features
- eBPF-based auto-instrumentation
- No code changes required
- HTTP and service telemetry
- OpenTelemetry support
- Prometheus-friendly metrics
- Kubernetes-friendly deployment
- Works well with Grafana ecosystem
Pros
- Good fit for open-source observability teams
- Reduces manual instrumentation effort
- Works well with Grafana and Prometheus
Cons
- More observability-focused than security-focused
- May not replace complete APM platforms
- Requires technical setup and tuning
Platforms / Deployment
Linux / Kubernetes / Cloud / Self-hosted / Hybrid
Security & Compliance
Not publicly stated.
Integrations & Ecosystem
Beyla fits naturally into Grafana and OpenTelemetry environments.
- Grafana
- Prometheus
- OpenTelemetry
- Kubernetes
- Linux workloads
- Cloud-native monitoring stacks
Support & Community
Grafana Beyla benefits from Grafana ecosystem documentation and open-source community support. Commercial support may depend on Grafana deployment choices.
#10 — Groundcover
Short description :
Groundcover is an eBPF-based observability platform designed for modern cloud-native and Kubernetes environments. It helps teams collect telemetry with low overhead and reduce the need for heavy manual instrumentation. Groundcover is useful for infrastructure monitoring, application performance visibility, and troubleshooting containerized workloads. It is best for teams that want practical observability without building a large monitoring stack from scratch. It fits SRE, DevOps, and platform teams.
Key Features
- eBPF-based observability
- Kubernetes visibility
- Application performance monitoring
- Infrastructure metrics
- Logs and traces support
- Low-overhead telemetry
- Production troubleshooting workflows
Pros
- Strong focus on eBPF-based observability
- Useful for Kubernetes-heavy teams
- Faster setup than some traditional monitoring stacks
Cons
- Smaller ecosystem than larger observability vendors
- Runtime security depth may be limited compared with security-first tools
- Public ratings are not confidently known
Platforms / Deployment
Linux / Kubernetes / Cloud / Hybrid
Security & Compliance
Not publicly stated.
Integrations & Ecosystem
Groundcover is built for modern cloud-native observability workflows.
- Kubernetes
- Cloud infrastructure
- OpenTelemetry workflows
- Dashboards and alerts
- DevOps pipelines
- Incident response processes
Support & Community
Groundcover provides vendor documentation and support. Public community size is smaller than older open-source projects.
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Cilium | Kubernetes networking and security | Linux / Kubernetes | Self-hosted / Hybrid | eBPF-powered networking and Hubble visibility | N/A |
| Falco | Runtime threat detection | Linux / Kubernetes / Containers | Self-hosted / Hybrid | Rule-based runtime security detection | N/A |
| Pixie | Kubernetes debugging and auto-telemetry | Linux / Kubernetes | Cloud / Self-hosted / Hybrid | No-code Kubernetes observability | N/A |
| Tetragon | Runtime security and workload visibility | Linux / Kubernetes | Self-hosted / Hybrid | Process, network, and file event monitoring | N/A |
| Datadog | Unified observability and cloud security | Web / Linux / Windows / macOS | Cloud / Hybrid | Full-stack monitoring and security context | N/A |
| Sysdig Secure | Container and Kubernetes runtime security | Linux / Kubernetes | Cloud / Hybrid | Runtime threat detection for cloud-native workloads | N/A |
| Aqua Security | Enterprise cloud-native security | Linux / Kubernetes | Cloud / Self-hosted / Hybrid | Build-to-runtime security coverage | N/A |
| New Relic | Developer-friendly observability | Web / Linux / Windows / macOS | Cloud / Hybrid | APM, logs, metrics, and Kubernetes visibility | N/A |
| Grafana Beyla | Open-source auto-instrumentation | Linux / Kubernetes | Self-hosted / Hybrid | eBPF-based OpenTelemetry signals | N/A |
| Groundcover | eBPF observability for Kubernetes | Linux / Kubernetes | Cloud / Hybrid | Low-overhead cloud-native telemetry | N/A |
Evaluation & eBPF Observability & Runtime Security Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Cilium | 9 | 7 | 9 | 9 | 9 | 9 | 9 | 8.65 |
| Falco | 8 | 7 | 8 | 9 | 8 | 8 | 9 | 8.05 |
| Pixie | 8 | 8 | 8 | 7 | 8 | 7 | 8 | 7.75 |
| Tetragon | 8 | 7 | 8 | 9 | 8 | 7 | 8 | 7.85 |
| Datadog | 9 | 8 | 10 | 8 | 8 | 9 | 7 | 8.45 |
| Sysdig Secure | 9 | 8 | 9 | 9 | 8 | 8 | 7 | 8.35 |
| Aqua Security | 9 | 7 | 9 | 9 | 8 | 8 | 7 | 8.20 |
| New Relic | 8 | 8 | 9 | 7 | 8 | 8 | 7 | 7.90 |
| Grafana Beyla | 7 | 7 | 8 | 6 | 8 | 7 | 9 | 7.45 |
| Groundcover | 8 | 8 | 8 | 7 | 8 | 7 | 8 | 7.75 |
The scores are comparative and should not be treated as fixed rankings for every company. A security team may score Falco, Tetragon, Sysdig, or Aqua higher based on runtime threat detection needs. A platform team may prefer Cilium for networking and Kubernetes visibility. A developer-focused team may prefer Pixie, New Relic, Datadog, Grafana Beyla, or Groundcover for faster troubleshooting.
Which eBPF Observability & Runtime Security Tools Should You Choose?
Solo / Freelancer
Solo engineers usually do not need a heavy enterprise platform. A good starting point is open-source tooling that helps build practical skills.
Recommended options:
- Falco for runtime security learning
- Grafana Beyla for auto-instrumentation
- Cilium for Kubernetes networking practice
- Pixie for Kubernetes debugging
Choose simple tools first and avoid complex enterprise platforms unless needed for client work.
SMB
Small and medium businesses should focus on easy setup, useful alerts, and low maintenance.
Recommended options:
- Datadog for unified observability
- New Relic for developer-friendly monitoring
- Groundcover for eBPF-based Kubernetes visibility
- Falco if runtime security is a priority
SMBs should avoid overengineering. Start with visibility, then add security policies.
Mid-Market
Mid-market teams usually need a mix of observability, runtime detection, and integrations.
Recommended options:
- Sysdig Secure for Kubernetes runtime security
- Datadog for broad observability and security context
- Cilium for Kubernetes networking and policy
- Aqua Security for cloud-native protection
- New Relic for application performance monitoring
Mid-market companies should validate integrations with CI/CD, SIEM, cloud, and incident tools.
Enterprise
Enterprises need scalability, security governance, access control, auditability, support, and deep integrations.
Recommended options:
- Cilium for platform networking and policy enforcement
- Sysdig Secure for runtime security
- Aqua Security for full cloud-native application protection
- Datadog for unified observability
- Tetragon for deep runtime visibility
Enterprises should run pilots across real clusters before standardizing.
Budget vs Premium
Budget-focused teams should consider open-source tools first. Falco, Cilium, Tetragon, Pixie, and Grafana Beyla can provide strong value when the team has technical skills.
Premium platforms are better when teams need:
- Managed support
- Central dashboards
- Compliance workflows
- Easier onboarding
- Enterprise integrations
- Security reporting
Feature Depth vs Ease of Use
If you need deep control, Cilium, Tetragon, Falco, Sysdig, and Aqua provide strong security and runtime capabilities. If you need ease of use, Datadog, New Relic, Groundcover, and Pixie may be easier for everyday troubleshooting.
Choose depth when security risk is high. Choose ease when developer adoption matters most.
Integrations & Scalability
Large environments should prioritize integrations with Kubernetes, cloud platforms, SIEM, CI/CD, Prometheus, Grafana, OpenTelemetry, and incident tools.
Best fit for integrations:
- Datadog
- New Relic
- Sysdig Secure
- Aqua Security
- Cilium
- Grafana Beyla
Scalability depends on cluster size, telemetry volume, retention needs, and alerting design.
Security & Compliance Needs
Security-heavy teams should prioritize runtime detection, policy enforcement, audit logs, RBAC, SIEM integration, and alert investigation workflows.
Best fit for security needs:
- Falco
- Tetragon
- Sysdig Secure
- Aqua Security
- Cilium
For compliance-driven teams, commercial platforms may be easier because they provide reporting, support, and governance features.
Frequently Asked Questions
1. What are eBPF Observability & Runtime Security Tools?
They are tools that use eBPF to collect low-level system, network, process, and container signals from Linux systems. They help teams monitor performance, troubleshoot issues, and detect runtime threats.
2. Why is eBPF important for Kubernetes?
Kubernetes workloads are dynamic and short-lived. eBPF helps capture real-time activity from pods, containers, services, and network flows without requiring heavy code changes.
3. Are eBPF tools only for security teams?
No. SRE, DevOps, platform, and developer teams also use eBPF tools for observability, debugging, network visibility, and performance troubleshooting.
4. Do eBPF tools replace traditional monitoring?
Not always. They often complement APM, logs, metrics, traces, and SIEM tools. eBPF adds deeper runtime and kernel-level visibility.
5. Are eBPF tools difficult to deploy?
Some are simple, while others require Kubernetes, Linux, networking, or security knowledge. Commercial tools are usually easier to onboard, while open-source tools may require more tuning.
6. What are common mistakes when adopting eBPF tools?
Common mistakes include enabling too much telemetry, ignoring alert tuning, not involving platform teams, skipping performance testing, and treating runtime security as a one-time setup.
7. Can eBPF tools improve runtime security?
Yes. They can detect suspicious processes, unexpected network connections, privilege changes, file access, and container escape behavior. The quality depends on rules, policies, and tuning.
8. Do eBPF tools create performance overhead?
Most eBPF tools are designed for low overhead, but overhead still depends on configuration, event volume, cluster size, and telemetry retention. Teams should test in staging before production rollout.
9. Which tool is best for open-source users?
Cilium, Falco, Tetragon, Pixie, and Grafana Beyla are strong choices for open-source-focused teams. The best choice depends on whether the priority is networking, security, or observability.
10. Which tool is best for enterprises?
Enterprises often shortlist Cilium, Sysdig Secure, Aqua Security, Datadog, and New Relic. The best option depends on whether the main need is networking, runtime security, compliance, or full-stack observability.
Conclusion
eBPF Observability & Runtime Security Tools are becoming important because modern cloud-native systems are complex, fast, and difficult to monitor with traditional methods alone. The best tool depends on your use case. Cilium is excellent for Kubernetes networking and policy. Falco and Tetragon are strong for runtime security. Pixie, Grafana Beyla, and Groundcover are useful for eBPF-based observability. Datadog and New Relic are better for teams that want broad commercial observability platforms. Sysdig and Aqua are strong for cloud-native security programs.