Introduction
Secure Software Supply Chain Attestation Tools help teams prove what software was built, how it was built, who built it, what source code was used, which dependencies were included, and whether the artifact can be trusted. In simple words, these tools create proof around software builds so organizations can reduce the risk of tampered code, hidden malware, dependency attacks, and unverified releases.
This category is closely connected with SLSA, provenance, SBOM, artifact signing, CI/CD security, container security, policy enforcement, and compliance reporting. As software teams use more open-source packages, automation pipelines, containers, AI coding assistants, and cloud-native deployment models, supply chain trust has become a core security requirement.
Real-world use cases include:
- Generating provenance for software builds
- Signing container images and artifacts
- Creating SBOMs for dependency visibility
- Enforcing trusted build policies in CI/CD
- Verifying artifacts before production deployment
Buyers should evaluate:
- SLSA and provenance support
- Artifact signing and verification
- SBOM generation and management
- CI/CD integration
- Container and Kubernetes support
- Policy enforcement
- Developer experience
- Audit logs and compliance reporting
- Open-source ecosystem maturity
- Enterprise support and scalability
Best for: DevSecOps teams, platform engineers, security architects, compliance teams, software vendors, cloud-native teams, open-source maintainers, and enterprises that need trusted release pipelines.
Not ideal for: very small projects with no formal CI/CD process, teams that do not publish artifacts, or simple internal scripts where manual review is enough. In those cases, basic version control, dependency scanning, and access control may be sufficient.
Key Trends in Secure Software Supply Chain Attestation Tools
- SLSA adoption is becoming more practical as organizations want structured levels of build integrity and provenance.
- Provenance is moving into CI/CD pipelines so teams can automatically capture how artifacts were built.
- SBOMs are becoming a standard expectation for software vendors, enterprise buyers, and regulated industries.
- Artifact signing is now a normal DevSecOps control for container images, packages, binaries, and deployment manifests.
- Keyless signing is gaining adoption because it reduces the burden of managing long-lived signing keys.
- Policy-as-code is becoming important for verifying artifacts before deployment.
- AI-generated code increases supply chain risk because teams need better dependency visibility and stronger build validation.
- Kubernetes admission control is a key enforcement point for blocking unsigned or untrusted workloads.
- Open-source security tooling is widely used, but enterprises often need support, governance, dashboards, and audit workflows.
- Provenance, SBOM, and vulnerability data are converging into broader software trust platforms.
How We Selected These Tools
The following tools were selected based on practical supply chain security value:
- Strong relevance to SLSA, provenance, SBOM, signing, or verification
- Adoption in DevSecOps, cloud-native, or open-source ecosystems
- CI/CD and container workflow compatibility
- Security posture and artifact trust capabilities
- Developer usability and automation support
- Policy enforcement and audit-readiness
- Support for modern software delivery pipelines
- Open-source maturity or enterprise platform credibility
- Fit across startups, SMBs, mid-market, and enterprise teams
- Ability to improve real-world supply chain security outcomes
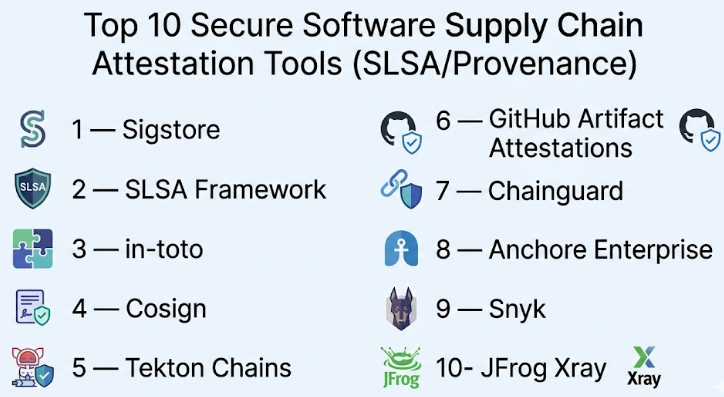
Top 10 Secure Software Supply Chain Attestation Tools
#1 — Sigstore
Short description :
Sigstore is a widely recognized open-source ecosystem for signing, verifying, and protecting software artifacts.It is commonly used for keyless signing, transparency logs, and artifact trust workflows.
Sigstore is especially useful for teams that want to prove software authenticity without managing traditional signing keys manually.It supports modern DevSecOps pipelines where artifact identity and build provenance are important.It is a strong choice for open-source projects, cloud-native teams, and enterprise software producers.
Key Features
- Keyless signing support
- Artifact signing and verification
- Transparency log support
- CI/CD-friendly workflows
- Container image signing support
- Identity-based trust model
- Strong open-source ecosystem adoption
Pros
- Reduces complexity around signing keys
- Strong fit for modern DevSecOps pipelines
- Useful for open-source and enterprise software trust
Cons
- Requires teams to understand signing and verification workflows
- Enterprise governance may need additional tooling
- Policy enforcement often requires integration with other tools
Platforms / Deployment
Linux / macOS / Windows
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports software signing, verification, transparency logs, and identity-based signing workflows.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
Sigstore fits well with CI/CD systems, container registries, Kubernetes policy tools, and artifact verification workflows.
- GitHub Actions
- Kubernetes policy engines
- Container registries
- OCI artifacts
- CI/CD pipelines
- Open-source release workflows
Support & Community
Sigstore has a strong open-source community and broad cloud-native ecosystem awareness. Enterprise support depends on vendor adoption and internal implementation model.
#2 — SLSA Framework
Short description :
SLSA is not a single tool, but it is one of the most important frameworks for secure software supply chain attestation.It helps teams define levels of build integrity, source control protection, provenance, and tamper resistance.SLSA is useful for organizations that want a structured roadmap for improving software build trust.
It works best when combined with CI/CD systems, provenance generators, signing tools, and policy engines.
It is valuable for teams that need clear security maturity goals.
Key Features
- Supply chain security maturity model
- Provenance-focused guidance
- Build integrity requirements
- Source and dependency control practices
- CI/CD hardening guidance
- Tamper-resistance expectations
- Practical alignment for secure release pipelines
Pros
- Provides a clear security improvement roadmap
- Helps teams standardize build trust practices
- Useful for audits, governance, and engineering alignment
Cons
- Not a standalone product
- Requires other tools for implementation
- Can feel complex without DevSecOps maturity
Platforms / Deployment
Varies / N/A
Security & Compliance
SLSA provides guidance for provenance, build security, and supply chain integrity.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
SLSA is usually implemented through build systems, CI/CD platforms, signing tools, provenance tools, and policy enforcement layers.
- CI/CD platforms
- Build systems
- Provenance generators
- Artifact signing tools
- Policy-as-code engines
- Security governance workflows
Support & Community
SLSA has strong recognition in the software supply chain security community. Support depends on internal security teams, consultants, or tool vendors implementing SLSA-aligned controls.
#3 — in-toto
Short description :
in-toto is a software supply chain security framework that helps verify each step of the software delivery process.It focuses on metadata, layout, verification, and ensuring that expected build steps happened correctly.in-toto is useful for teams that need detailed evidence about how software was produced.
It supports provenance-style workflows and can help detect unauthorized changes in the build process.
It is a strong option for security-focused engineering teams.
Key Features
- Supply chain metadata generation
- Build step verification
- Provenance support
- Layout-based policy definition
- Tamper detection
- Integration with signing workflows
- Strong fit for secure release pipelines
Pros
- Strong evidence model for build steps
- Useful for high-trust software delivery
- Works well with signing and provenance practices
Cons
- Requires careful setup and process design
- May be complex for smaller teams
- Best suited for mature engineering workflows
Platforms / Deployment
Linux / macOS / Windows
Self-hosted / Hybrid
Security & Compliance
Supports signed metadata and supply chain verification concepts.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
in-toto is often used with CI/CD systems, build pipelines, artifact signing workflows, and SLSA-aligned provenance systems.
- CI/CD tools
- Build systems
- Signing tools
- Release pipelines
- Policy verification workflows
- Provenance metadata systems
Support & Community
in-toto has strong credibility in software supply chain security. Community support is solid, but implementation may require security engineering knowledge.
#4 — Cosign
Short description :
Cosign is a popular tool for signing and verifying container images and other software artifacts.
It is part of the broader Sigstore ecosystem and is commonly used in cloud-native security workflows.
Cosign helps teams ensure that only trusted artifacts are deployed into environments such as Kubernetes.
It is useful for DevSecOps teams that want practical artifact signing without heavy complexity.
It works well for container-first organizations and platform teams.
Key Features
- Container image signing
- Artifact verification
- Keyless signing support
- OCI artifact support
- CI/CD pipeline integration
- Kubernetes admission policy compatibility
- Provenance and attestation support
Pros
- Strong fit for container image trust
- Practical and developer-friendly
- Works well with modern cloud-native workflows
Cons
- Requires policy tools for strong enforcement
- Keyless workflows need identity understanding
- Not a complete supply chain platform alone
Platforms / Deployment
Linux / macOS / Windows
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports artifact signing, verification, and attestations.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
Cosign integrates naturally with container registries, CI/CD systems, Kubernetes, and policy enforcement tools.
- Container registries
- Kubernetes
- CI/CD pipelines
- OCI artifacts
- Policy engines
- Sigstore ecosystem
Support & Community
Cosign has strong cloud-native community usage and practical documentation. Enterprise support depends on vendor, platform, or internal security operations.
#5 — Tekton Chains
Short description :
Tekton Chains is a supply chain security component for Tekton pipelines.
It helps generate, sign, and store provenance and attestation metadata for build artifacts.
It is especially useful for teams already using Tekton for Kubernetes-native CI/CD.
Tekton Chains supports modern software supply chain security practices around build transparency.
It is a good fit for cloud-native platform teams building secure pipelines.
Key Features
- CI/CD provenance generation
- Artifact signing support
- Tekton pipeline integration
- SLSA-oriented workflows
- Kubernetes-native design
- Attestation metadata capture
- Container build trust support
Pros
- Strong fit for Tekton users
- Useful for Kubernetes-native pipelines
- Helps automate provenance generation
Cons
- Less useful outside Tekton environments
- Requires Kubernetes and Tekton familiarity
- May need additional policy tooling
Platforms / Deployment
Linux / Kubernetes
Self-hosted / Hybrid
Security & Compliance
Supports signed provenance and attestation workflows in Tekton pipelines.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
Tekton Chains is tightly connected to Tekton and Kubernetes-native CI/CD workflows.
- Tekton Pipelines
- Kubernetes
- Container registries
- Signing tools
- SLSA workflows
- Policy engines
Support & Community
Tekton Chains benefits from the Tekton and cloud-native ecosystem. Support quality depends on internal platform maturity and vendor involvement.
#6 — GitHub Artifact Attestations
Short description :
GitHub Artifact Attestations help teams create trusted provenance for artifacts built through GitHub Actions.
It is useful for organizations already using GitHub as their main source control and CI/CD platform.
The tool helps prove that an artifact came from a specific workflow and repository context.
It supports modern software supply chain requirements around build origin and verification.
It is a practical option for teams that want attestation without building everything manually.
Key Features
- Artifact provenance generation
- GitHub Actions integration
- Build identity association
- Attestation verification workflows
- Developer-friendly automation
- Useful for release pipelines
- Strong fit for GitHub-native teams
Pros
- Easy adoption for GitHub Actions users
- Reduces manual provenance setup
- Useful for trusted release automation
Cons
- Best suited to GitHub-based workflows
- Limited value for non-GitHub CI/CD environments
- Advanced governance may need extra tools
Platforms / Deployment
Cloud
GitHub-hosted / Hybrid workflow usage
Security & Compliance
Supports provenance and artifact attestation workflows.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
GitHub Artifact Attestations work best inside GitHub Actions and release workflows.
- GitHub Actions
- GitHub repositories
- Release pipelines
- Package publishing workflows
- Artifact verification workflows
- DevSecOps automation
Support & Community
Support depends on GitHub platform support and documentation. Community adoption is growing among GitHub-native engineering teams.
#7 — Chainguard
Short description :
Chainguard provides secure software supply chain solutions focused on hardened container images, provenance, SBOMs, and trusted software delivery.
It is useful for enterprises that want to reduce open-source and container image risk.
Chainguard is especially relevant for teams that need verified, minimal, and security-focused base images.
It helps organizations improve trust across build and deployment pipelines.
It is a strong option for security-conscious cloud-native companies.
Key Features
- Hardened container images
- SBOM support
- Provenance support
- Supply chain security platform capabilities
- Container security workflows
- Enterprise-oriented controls
- Cloud-native focus
Pros
- Strong enterprise supply chain security positioning
- Useful for reducing container base image risk
- Good fit for cloud-native security teams
Cons
- May be more than small teams need
- Pricing and commercial details vary
- Requires integration into existing workflows
Platforms / Deployment
Cloud / Hybrid
Linux / Container environments
Security & Compliance
Security-focused platform with SBOM and provenance-related capabilities.
Specific compliance certifications: Not publicly stated
Integrations & Ecosystem
Chainguard fits into container build, registry, CI/CD, and Kubernetes workflows.
- Container registries
- Kubernetes
- CI/CD pipelines
- SBOM workflows
- Image scanning workflows
- DevSecOps platforms
Support & Community
Chainguard is enterprise-oriented and offers commercial support models. Community visibility is strong in software supply chain security conversations.
#8 — Anchore Enterprise
Short description :
Anchore Enterprise is a container and software supply chain security platform focused on SBOMs, vulnerability management, policy, and compliance.It helps teams understand what is inside software artifacts and whether they meet security requirementsAnchore is useful for organizations that need governance around containers and software components.It supports enterprise workflows where auditability and policy enforcement matter.It is a good fit for security, compliance, and platform engineering teams.
Key Features
- SBOM generation and management
- Container image analysis
- Vulnerability scanning
- Policy enforcement
- Compliance reporting
- CI/CD integration
- Enterprise governance workflows
Pros
- Strong SBOM and policy management capabilities
- Useful for regulated or audit-heavy environments
- Good fit for enterprise container security programs
Cons
- May require implementation planning
- Can be more platform-heavy than lightweight tools
- Pricing varies by enterprise requirements
Platforms / Deployment
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports security scanning, SBOM, policy, and compliance workflows.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
Anchore integrates with container registries, CI/CD systems, Kubernetes, and enterprise security workflows.
- CI/CD platforms
- Container registries
- Kubernetes
- Ticketing workflows
- Security dashboards
- Compliance reporting systems
Support & Community
Anchore has enterprise support options and strong documentation. Community support is also available around its open-source ecosystem.
#9 — Snyk
Short description :
Snyk is a developer-first security platform that helps teams find and fix vulnerabilities across code, dependencies, containers, and infrastructure.
While it is broader than attestation alone, it is relevant to software supply chain security because it improves dependency visibility and risk control.
Snyk is useful for teams that want developer-friendly security scanning inside CI/CD workflows.
It helps reduce risk before artifacts reach production.
It is a strong fit for teams that prioritize developer adoption and fast remediation.
Key Features
- Open-source dependency scanning
- Container security scanning
- Infrastructure-as-code scanning
- Developer workflow integration
- CI/CD integration
- Vulnerability prioritization
- Fix guidance
Pros
- Strong developer experience
- Broad security coverage across modern stacks
- Useful for early risk detection
Cons
- Not a dedicated provenance tool
- Attestation workflows may require other tools
- Pricing can vary by scale and features
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Supports vulnerability management and security workflow controls.
Specific attestation compliance certifications: Not publicly stated
Integrations & Ecosystem
Snyk integrates deeply with developer tools, repositories, CI/CD systems, and container workflows.
- Source code repositories
- CI/CD platforms
- Container registries
- IDEs
- Issue trackers
- Cloud-native workflows
Support & Community
Snyk has strong documentation, commercial support, and developer community adoption. Support levels depend on plan and organization needs.
#10 — JFrog Xray
Short description :
JFrog Xray is a software composition analysis and artifact security tool commonly used with JFrog Artifactory.
It helps teams scan artifacts, containers, packages, and dependencies for vulnerabilities and license risks.
While it is not only an attestation tool, it plays an important role in trusted software release pipelines.
It is useful for organizations that manage large artifact repositories and need policy-based governance.
It is a strong option for enterprises already using the JFrog ecosystem.
Key Features
- Artifact and dependency scanning
- Container image analysis
- License risk detection
- Policy enforcement
- Artifactory integration
- CI/CD security workflows
- Enterprise reporting
Pros
- Strong fit for artifact-heavy enterprises
- Works well with repository management workflows
- Good governance and policy capabilities
Cons
- Best value inside the JFrog ecosystem
- Not a pure SLSA provenance solution
- May require enterprise setup and administration
Platforms / Deployment
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports vulnerability scanning, license analysis, and policy workflows.
SOC 2, ISO 27001, HIPAA: Not publicly stated
Integrations & Ecosystem
JFrog Xray is strongest when used with Artifactory and enterprise DevSecOps pipelines.
- JFrog Artifactory
- CI/CD platforms
- Container registries
- Package repositories
- Security dashboards
- Release governance workflows
Support & Community
JFrog offers enterprise support and documentation. Community strength is high among organizations already using JFrog for artifact management.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Sigstore | Keyless artifact signing | Linux, macOS, Windows | Cloud / Self-hosted / Hybrid | Keyless signing and transparency logs | N/A |
| SLSA Framework | Supply chain maturity model | Varies / N/A | Varies / N/A | Structured build integrity guidance | N/A |
| in-toto | Supply chain step verification | Linux, macOS, Windows | Self-hosted / Hybrid | Signed metadata and process verification | N/A |
| Cosign | Container image signing | Linux, macOS, Windows | Cloud / Self-hosted / Hybrid | Practical artifact signing and verification | N/A |
| Tekton Chains | Tekton-based provenance | Linux / Kubernetes | Self-hosted / Hybrid | CI/CD provenance for Tekton pipelines | N/A |
| GitHub Artifact Attestations | GitHub Actions provenance | Cloud | Cloud / Hybrid | Native GitHub artifact attestation | N/A |
| Chainguard | Secure container supply chain | Linux / Containers | Cloud / Hybrid | Hardened images with supply chain focus | N/A |
| Anchore Enterprise | SBOM and container governance | Cloud / Self-hosted | Cloud / Self-hosted / Hybrid | SBOM and policy management | N/A |
| Snyk | Developer-first supply chain risk scanning | Cloud / Developer tools | Cloud / Hybrid | Dependency and container risk detection | N/A |
| JFrog Xray | Artifact repository security | Cloud / Self-hosted | Cloud / Self-hosted / Hybrid | Artifact scanning and policy enforcement | N/A |
Evaluation & Secure Software Supply Chain Attestation Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Sigstore | 9 | 7 | 8 | 9 | 8 | 8 | 9 | 8.30 |
| SLSA Framework | 8 | 6 | 7 | 9 | 7 | 7 | 9 | 7.65 |
| in-toto | 8 | 6 | 7 | 9 | 8 | 7 | 8 | 7.60 |
| Cosign | 9 | 8 | 8 | 9 | 8 | 8 | 9 | 8.45 |
| Tekton Chains | 8 | 6 | 8 | 8 | 8 | 7 | 8 | 7.60 |
| GitHub Artifact Attestations | 8 | 9 | 8 | 8 | 8 | 8 | 8 | 8.10 |
| Chainguard | 9 | 8 | 8 | 9 | 8 | 9 | 7 | 8.30 |
| Anchore Enterprise | 8 | 7 | 8 | 8 | 8 | 9 | 7 | 7.80 |
| Snyk | 7 | 9 | 9 | 8 | 8 | 9 | 7 | 8.00 |
| JFrog Xray | 8 | 7 | 9 | 8 | 8 | 9 | 7 | 8.00 |
These scores are comparative and should be used as a starting point, not a final buying decision. A dedicated signing tool may score higher for attestation, while a broader platform may score higher for governance. Teams should match scores to their real workflow: CI/CD, containers, SBOM, Kubernetes, compliance, or developer security. Always run a pilot before choosing a production standard.
Which Secure Software Supply Chain Attestation Tools
Solo / Freelancer
Solo developers should keep the setup simple. Cosign and Sigstore are practical choices for signing and verifying artifacts. If the project is hosted and built through GitHub, GitHub Artifact Attestations can be easier to start with. For dependency risk visibility, Snyk can help identify common open-source issues.
SMB
SMBs should focus on practical controls that reduce risk without creating too much process burden. A good starting stack may include Cosign for signing, GitHub Artifact Attestations for provenance if using GitHub Actions, and Snyk or Anchore for dependency and container visibility. SMBs should avoid overengineering early and start with the most critical release pipelines.
Mid-Market
Mid-market companies usually need more governance, reporting, and repeatable CI/CD controls. Sigstore, Cosign, Anchore Enterprise, Snyk, and JFrog Xray can fit well depending on the existing toolchain. If the team uses Tekton, Tekton Chains is a strong option for generating provenance in Kubernetes-native pipelines.
Enterprise
Enterprises should focus on policy enforcement, audit evidence, SBOM management, artifact trust, and scalable governance. Chainguard, Anchore Enterprise, JFrog Xray, Sigstore, and in-toto are strong candidates depending on the maturity of the DevSecOps program. Enterprises should also align internal standards with the SLSA Framework to define maturity goals.
Budget vs Premium
Open-source tools such as Sigstore, Cosign, in-toto, and SLSA can reduce licensing cost, but they require skilled implementation. Premium platforms such as Chainguard, Anchore Enterprise, Snyk, and JFrog Xray may reduce operational burden with dashboards, reporting, support, and enterprise governance.
Feature Depth vs Ease of Use
For deep attestation and supply chain verification, in-toto, Sigstore, and SLSA are strong. For easier artifact signing, Cosign is practical. For broader developer security, Snyk is easier for development teams. For enterprise artifact governance, JFrog Xray and Anchore Enterprise provide more complete management workflows.
Integrations & Scalability-
If your company already uses GitHub Actions, GitHub Artifact Attestations is a natural fit. If your pipelines are Kubernetes-native with Tekton, Tekton Chains is better aligned. If your organization relies heavily on container images and registries, Cosign, Chainguard, Anchore, and JFrog Xray should be evaluated carefully.
Security & Compliance Needs
For compliance-heavy environments, prioritize provenance, SBOM, audit logs, artifact verification, access control, policy enforcement, and reporting. Do not choose a tool only because it supports signing. The full process should prove source integrity, build integrity, dependency visibility, artifact authenticity, and deployment trust.
Frequently Asked Questions (FAQs)
1. What is software supply chain attestation?
Software supply chain attestation is proof about how software was created, built, signed, and released. It helps teams verify that an artifact came from a trusted source and followed an expected build process.
2. What is SLSA in software supply chain security?
SLSA is a framework that helps organizations improve software build integrity and supply chain trust. It gives teams a structured way to think about source protection, build security, provenance, and tamper resistance.
3. What is provenance in software builds?
Provenance is metadata that explains where a software artifact came from and how it was built. It may include source repository details, build workflow information, builder identity, and artifact output data.
4. Is SBOM the same as attestation?
No. An SBOM lists software components and dependencies. Attestation proves facts about the build or artifact. Both are important, but they solve different parts of software supply chain security.
5. Why is artifact signing important?
Artifact signing helps prove that software has not been tampered with after it was created. It allows teams to verify trust before deployment, especially for containers, binaries, and packages.
6. Are open-source attestation tools enough for enterprises?
They can be enough for some teams, but enterprises often need reporting, support, dashboards, access control, policy enforcement, and audit workflows. Many enterprises use open-source tools with commercial platforms.
7. What is keyless signing?
Keyless signing allows developers or systems to sign artifacts using identity-based workflows instead of managing long-lived private keys. It can reduce key management risk when implemented correctly.
8. How do these tools integrate with CI/CD?
Most tools integrate through pipeline steps, build metadata capture, artifact signing commands, policy checks, or release gates. The exact setup depends on the CI/CD platform and artifact type.
9. What are common mistakes when implementing supply chain attestation?
Common mistakes include signing artifacts without verifying them later, generating SBOMs but not using them, ignoring policy enforcement, and failing to protect the CI/CD pipeline itself.
10. Can attestation tools stop all supply chain attacks?
No tool can stop every attack. Attestation tools reduce risk by improving visibility, trust, verification, and auditability. They should be combined with access control, scanning, secrets management, and secure build practices.
Conclusion
Secure Software Supply Chain Attestation Tools are now essential for organizations that want stronger confidence in their software delivery process. The best tool depends on the team’s current stack, maturity, and risk level. Cosign and Sigstore are strong for signing and verification, in-toto and SLSA help with structured provenance and build integrity, Tekton Chains fits Kubernetes-native CI/CD, and GitHub Artifact Attestations works well for GitHub-based teams. Broader platforms such as Chainguard, Anchore Enterprise, Snyk, and JFrog Xray help with SBOM, scanning, governance, and enterprise controls.