Introduction
Vulnerability Assessment Tools are cybersecurity solutions that help organizations identify, analyze, and prioritize security weaknesses across systems, networks, applications, and cloud environments. In simple terms, these tools scan your infrastructure to find vulnerabilities before attackers can exploit them.
As cyber threats continue to evolve, organizations are under constant pressure to detect and fix vulnerabilities quickly. Manual assessments are no longer enough—modern vulnerability assessment tools automate scanning, provide risk-based prioritization, and integrate with broader security workflows. This makes them a critical part of any proactive security strategy.
Common Use Cases
- Scanning networks and endpoints for vulnerabilities
- Identifying misconfigurations in cloud environments
- Web application security testing
- Compliance audits and reporting
- Risk prioritization and remediation tracking
What Buyers Should Evaluate
- Coverage (network, application, cloud, containers)
- Scan accuracy and false positive rates
- Risk scoring and prioritization
- Automation and scheduling capabilities
- Integration with SIEM, SOAR, DevOps tools
- Ease of deployment and usability
- Reporting and compliance features
- Scalability across environments
- Agent vs agentless scanning
- API and customization support
Best for: Security teams, DevSecOps engineers, IT administrators, enterprises, and organizations managing complex IT environments.
Not ideal for: Very small teams with minimal infrastructure, or organizations that only need basic antivirus or endpoint protection.
Key Trends in Customer IAM (CIAM)
- Risk-based vulnerability prioritization: Focus on exploitable vulnerabilities instead of raw counts
- AI-driven scanning and remediation suggestions
- Continuous monitoring vs periodic scanning
- Cloud and container security integration
- Shift-left security in DevOps pipelines
- Automated patch management integration
- Agentless scanning growth
- Unified vulnerability + exposure management platforms
- Integration with SOAR for automated remediation
- Compliance automation and reporting
How We Selected These Tools (Methodology)
- Evaluated market leadership and adoption
- Assessed scan coverage and accuracy
- Considered risk prioritization capabilities
- Reviewed integration ecosystem (SIEM, DevOps, cloud)
- Analyzed deployment flexibility (cloud/on-prem/agent-based)
- Evaluated ease of use and onboarding
- Considered performance and scalability
- Reviewed security and compliance features
- Assessed vendor support and community
- Included tools for enterprise and mid-market users
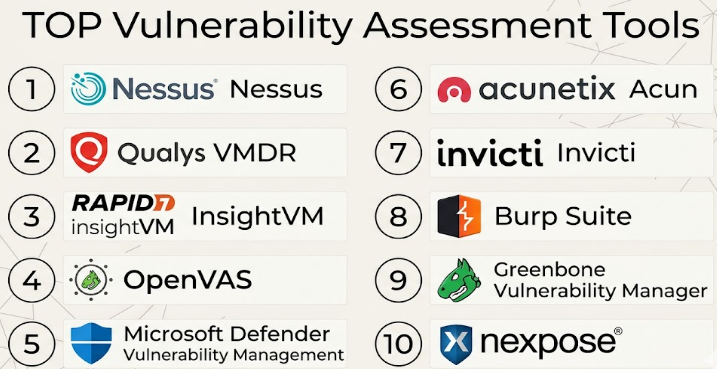
Top Vulnerability Assessment Tools
#1 — Tenable Nessus
Short description: One of the most widely used vulnerability scanners, ideal for security professionals and enterprises.
Key Features
- Comprehensive vulnerability scanning
- Plugin-based architecture
- Risk scoring and prioritization
- Configuration auditing
- Compliance checks
- Detailed reporting
Pros
- High accuracy and reliability
- Large vulnerability database
Cons
- Requires expertise
- Limited automation compared to platforms
Platforms / Deployment
Windows / Linux / macOS | Self-hosted
Security & Compliance
RBAC, encryption; others Not publicly stated
Integrations & Ecosystem
- SIEM tools
- APIs
- Security platforms
- Compliance tools
Support & Community
Strong community; extensive documentation
#2 — Qualys VMDR
Short description: Cloud-based vulnerability management platform with detection, response, and remediation capabilities.
Key Features
- Continuous vulnerability scanning
- Asset discovery
- Risk prioritization
- Patch management integration
- Cloud security support
- Compliance reporting
Pros
- Cloud-native scalability
- Unified platform approach
Cons
- UI complexity
- Pricing can be high
Platforms / Deployment
Cloud
Security & Compliance
SSO, RBAC, encryption; others Not publicly stated
Integrations & Ecosystem
- Cloud providers
- SIEM
- DevOps tools
- APIs
Support & Community
Enterprise support; good documentation
#3 — Rapid7 InsightVM
Short description: Vulnerability management tool focused on real-time risk visibility and remediation.
Key Features
- Live vulnerability monitoring
- Risk scoring
- Asset discovery
- Remediation workflows
- Integration with Rapid7 tools
- Reporting dashboards
Pros
- Real-time insights
- Strong analytics
Cons
- Requires tuning
- Moderate learning curve
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
SSO, RBAC; others Not publicly stated
Integrations & Ecosystem
- Insight platform
- SIEM tools
- APIs
Support & Community
Good support; active community
#4 — OpenVAS
Short description: Open-source vulnerability scanner suitable for organizations seeking a free solution.
Key Features
- Open-source scanning
- Network vulnerability detection
- Regular updates
- Custom scan configurations
- Reporting features
Pros
- Free to use
- Highly customizable
Cons
- Requires technical expertise
- Limited enterprise features
Platforms / Deployment
Linux | Self-hosted
Security & Compliance
Varies / N/A
Integrations & Ecosystem
- APIs
- Custom integrations
- Security tools
Support & Community
Strong open-source community
#5 — Microsoft Defender Vulnerability Management
Short description: Integrated vulnerability management solution within Microsoft security ecosystem.
Key Features
- Continuous vulnerability assessment
- Risk-based prioritization
- Integration with Defender tools
- Endpoint visibility
- Remediation guidance
Pros
- Seamless Microsoft integration
- Easy deployment
Cons
- Limited outside Microsoft ecosystem
- Requires Microsoft environment
Platforms / Deployment
Cloud
Security & Compliance
MFA, RBAC, encryption; others Not publicly stated
Integrations & Ecosystem
- Microsoft Defender
- Azure
- Security tools
Support & Community
Strong enterprise support
#6 — Acunetix
Short description: Web application vulnerability scanner designed for developers and security teams.
Key Features
- Web app scanning
- SQL injection detection
- Cross-site scripting detection
- Automated scanning
- Reporting tools
Pros
- Strong web scanning capabilities
- Easy to use
Cons
- Limited network scanning
- Pricing transparency limited
Platforms / Deployment
Windows / Linux / Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- CI/CD tools
- APIs
- Security tools
Support & Community
Good support; documentation available
#7 — Invicti
Short description: Advanced web vulnerability scanner with automation and integration capabilities.
Key Features
- Automated web scanning
- Proof-based scanning
- CI/CD integration
- Vulnerability verification
- Reporting
Pros
- High accuracy
- DevOps-friendly
Cons
- Expensive
- Focused on web apps
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- DevOps tools
- APIs
- Security platforms
Support & Community
Strong support
#8 — Burp Suite
Short description: Popular web security testing tool used by penetration testers.
Key Features
- Web vulnerability scanning
- Manual testing tools
- Proxy-based analysis
- Automation features
- Extensibility
Pros
- Industry standard for pentesting
- Highly flexible
Cons
- Steep learning curve
- Not beginner-friendly
Platforms / Deployment
Windows / macOS / Linux
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- Extensions
- APIs
- Security tools
Support & Community
Very strong community
#9 — Greenbone Vulnerability Manager
Short description: Open-source vulnerability management platform derived from OpenVAS.
Key Features
- Vulnerability scanning
- Management dashboards
- Reporting tools
- Custom configurations
- Regular updates
Pros
- Open-source
- Flexible
Cons
- Complex setup
- Limited enterprise features
Platforms / Deployment
Linux | Self-hosted
Security & Compliance
Varies / N/A
Integrations & Ecosystem
- APIs
- Security tools
- Custom integrations
Support & Community
Open-source community
#10 — Nexpose (Rapid7)
Short description: On-prem vulnerability scanner offering deep visibility and analytics.
Key Features
- Vulnerability scanning
- Risk scoring
- Asset discovery
- Reporting
- Integration with Insight platform
Pros
- Strong analytics
- Flexible deployment
Cons
- UI complexity
- Requires expertise
Platforms / Deployment
Windows / Linux | Self-hosted
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- Rapid7 tools
- APIs
- SIEM
Support & Community
Good support
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Nessus | Enterprises | Multi-OS | Self-hosted | Large plugin library | N/A |
| Qualys VMDR | Cloud-first orgs | Web | Cloud | Continuous monitoring | N/A |
| InsightVM | SOC teams | Web | Hybrid | Real-time risk | N/A |
| OpenVAS | Budget users | Linux | Self-hosted | Open-source | N/A |
| Defender VM | Microsoft users | Web | Cloud | Native integration | N/A |
| Acunetix | Web apps | Multi-OS | Hybrid | Web scanning | N/A |
| Invicti | DevOps teams | Web | Hybrid | Proof-based scanning | N/A |
| Burp Suite | Pentesters | Multi-OS | Desktop | Manual testing | N/A |
| Greenbone | Open-source users | Linux | Self-hosted | Flexibility | N/A |
| Nexpose | Enterprises | Multi-OS | Self-hosted | Deep analytics | N/A |
Vulnerability Assessment Tools Scoring
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Nessus | 9 | 7 | 8 | 8 | 9 | 9 | 7 | 8.3 |
| Qualys | 9 | 7 | 9 | 8 | 9 | 8 | 7 | 8.4 |
| InsightVM | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.9 |
| OpenVAS | 7 | 6 | 7 | 6 | 7 | 6 | 9 | 7.1 |
| Defender VM | 8 | 8 | 8 | 8 | 8 | 8 | 8 | 8.0 |
| Acunetix | 8 | 8 | 7 | 7 | 8 | 7 | 7 | 7.7 |
| Invicti | 9 | 7 | 8 | 7 | 8 | 8 | 6 | 7.9 |
| Burp Suite | 8 | 6 | 7 | 7 | 8 | 9 | 7 | 7.6 |
| Greenbone | 7 | 6 | 7 | 6 | 7 | 6 | 9 | 7.1 |
| Nexpose | 8 | 6 | 8 | 7 | 8 | 7 | 7 | 7.5 |
How to interpret scores:
These scores provide a relative comparison of tools based on features, usability, and value. Higher scores indicate stronger capabilities, but the best choice depends on your specific environment, team expertise, and security needs.
Which Service Mesh Platforms Is Right for You?
Solo / Freelancer
- Best: OpenVAS, Greenbone
- Focus on free and simple tools
SMB
- Best: Acunetix, InsightVM
- Balance ease of use and features
Mid-Market
- Best: Qualys, Invicti
- Focus on scalability and automation
Enterprise
- Best: Nessus, Qualys, Defender VM
- Focus on integration and compliance
Budget vs Premium
- Budget: OpenVAS, Greenbone
- Premium: Qualys, Invicti
Feature Depth vs Ease of Use
- Feature-rich: Nessus, Qualys
- Easy-to-use: Acunetix, Defender VM
Integrations & Scalability
- High integration: Qualys, InsightVM
- Moderate: OpenVAS
Security & Compliance Needs
- High compliance: Qualys, Defender
- Moderate: Acunetix
Vulnerability Assessment Tools FAQs
What is a vulnerability assessment tool?
It scans systems and applications to identify security weaknesses before attackers exploit them.
How much do these tools cost?
Pricing varies widely; open-source tools are free while enterprise solutions follow subscription models.
Are vulnerability scanners accurate?
Most are highly accurate, but false positives can occur and require validation.
How often should scans be run?
Continuous or scheduled weekly scans are recommended.
Can these tools integrate with DevOps?
Yes, many support CI/CD integration for shift-left security.
Are they suitable for cloud environments?
Yes, many tools support cloud and hybrid environments.
Do they support automation?
Yes, modern tools automate scanning and remediation workflows.
What are common mistakes?
Ignoring false positives and not prioritizing critical vulnerabilities.
Can they replace penetration testing?
No, they complement but do not replace manual testing.
Is it easy to switch tools?
Switching can be complex due to integrations and workflows.
Conclusion
Vulnerability Assessment Tools are a foundational component of any modern cybersecurity strategy, helping organizations identify and remediate weaknesses before they can be exploited. From enterprise-grade platforms like Qualys and Nessus to open-source options like OpenVAS and Greenbone, there are solutions for every type of organization. The right choice depends on your infrastructure, team expertise, and integration requirements. Instead of focusing only on features, evaluate how well the tool fits into your existing security ecosystem. Shortlist a few options, run pilot scans, and validate their accuracy and usability before making a final decision.