Introduction
Key Management Systems (KMS) are tools designed to create, store, manage, rotate, and protect cryptographic keys used for encrypting sensitive data. In simple terms, they act as the central authority for encryption keys, ensuring that your data remains secure whether it is stored, transmitted, or processed.
In the modern landscape of cloud-native applications, zero-trust security, and AI-driven systems, KMS has become a foundational security layer. With increasing cyber threats, stricter compliance requirements, and distributed architectures, organizations can no longer rely on manual or fragmented key management.
Real-world use cases include:
- Encrypting cloud storage and databases
- Securing API communications and microservices
- Managing TLS/SSL certificates and secrets
- Protecting sensitive customer and financial data
- Enabling secure DevOps pipelines and CI/CD processes
What buyers should evaluate:
- Key lifecycle management (creation, rotation, revocation)
- Access control (RBAC, IAM integration)
- Encryption standards and hardware-backed security
- Audit logging and compliance support
- Integration with cloud platforms and DevOps tools
- Scalability and performance
- Ease of use and automation capabilities
- Multi-region and disaster recovery support
Best for: IT managers, DevOps engineers, security teams, cloud architects, fintech companies, SaaS providers, and enterprises handling sensitive data.
Not ideal for: Small projects or static applications with minimal encryption needs, where simpler encryption libraries or basic secret managers may be sufficient.
Key Trends in Key Management Systems (KMS) Tools
- Cloud-native KMS dominance: Most organizations prefer managed KMS services integrated with cloud providers.
- AI-driven anomaly detection: Some platforms are introducing AI-based monitoring for suspicious key usage.
- Zero Trust security integration: KMS tools are aligning with identity-first and zero-trust architectures.
- Secrets + KMS convergence: Modern tools combine key management with secrets management.
- Multi-cloud and hybrid support: Increasing demand for unified KMS across AWS, Azure, and GCP.
- Hardware-backed security (HSM): Adoption of FIPS-compliant hardware security modules is growing.
- Automated key rotation: Default automated rotation policies are becoming standard.
- Compliance-first design: Built-in compliance features for GDPR, HIPAA, and financial regulations.
- API-first architecture: Developer-friendly APIs for seamless automation.
- Fine-grained access control: Integration with IAM and policy-based access systems.
How We Selected These Tools (Methodology)
- Evaluated market adoption and enterprise usage
- Reviewed core KMS capabilities and feature depth
- Assessed security architecture and compliance readiness
- Considered integration ecosystem and extensibility
- Analyzed performance and reliability signals
- Reviewed developer and operational usability
- Compared deployment flexibility (cloud vs self-hosted)
- Considered fit across SMB, mid-market, and enterprise
- Focused on real-world scalability and production readiness
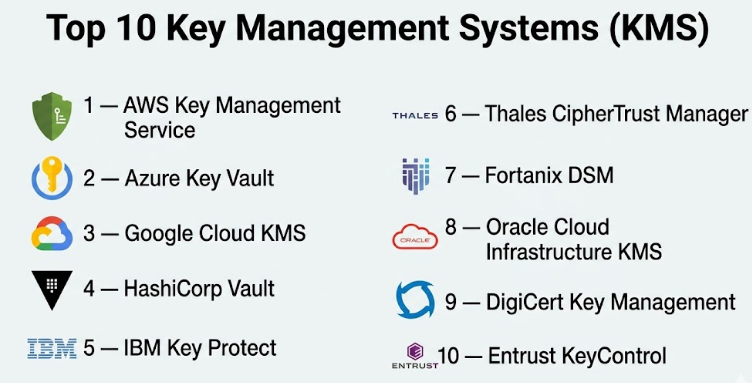
Top 10 Key Management Systems (KMS)
#1 — AWS Key Management Service
Short description: A fully managed KMS from AWS that allows users to create and control encryption keys integrated deeply with AWS services. Ideal for cloud-native applications running on AWS.
Key Features
- Centralized key management
- Automatic key rotation
- Integration with AWS services (S3, RDS, Lambda)
- Fine-grained IAM policies
- Hardware security module (HSM) backing
- Audit logs via CloudTrail
Pros
- Deep AWS ecosystem integration
- Highly scalable and reliable
Cons
- Limited multi-cloud support
- AWS lock-in risk
Platforms / Deployment
Cloud
Security & Compliance
Supports IAM, encryption, audit logs; compliance details not publicly stated in full.
Integrations & Ecosystem
Strong AWS-native ecosystem:
- S3, EC2, RDS
- Lambda
- CloudTrail
- IAM
Support & Community
Extensive documentation and enterprise-grade support.
#2 — Azure Key Vault
Short description: Microsoft’s KMS solution for managing keys, secrets, and certificates within Azure environments.
Key Features
- Key and secret storage
- Certificate management
- Integration with Azure services
- Role-based access control
- Hardware-backed key protection
Pros
- Seamless Azure integration
- Strong enterprise security features
Cons
- Azure-centric
- Learning curve for beginners
Platforms / Deployment
Cloud
Security & Compliance
RBAC, encryption, audit logs; compliance certifications not publicly stated.
Integrations & Ecosystem
- Azure AD
- Azure DevOps
- App Services
Support & Community
Strong Microsoft enterprise support.
#3 — Google Cloud KMS
Short description: A scalable KMS solution for encrypting and managing keys across Google Cloud services.
Key Features
- Centralized key control
- Automatic rotation
- IAM integration
- Cloud HSM support
- Envelope encryption
Pros
- Strong performance
- Developer-friendly APIs
Cons
- Limited outside GCP
- Less mature ecosystem than AWS
Platforms / Deployment
Cloud
Security & Compliance
IAM, encryption, audit logs; compliance details not publicly stated.
Integrations & Ecosystem
- BigQuery
- Compute Engine
- Cloud Storage
Support & Community
Good documentation and support.
#4 — HashiCorp Vault
Short description: A widely used secrets and key management platform designed for multi-cloud and hybrid environments.
Key Features
- Dynamic secrets
- Encryption as a service
- Token-based authentication
- Lease and revocation system
- Multi-cloud support
Pros
- Highly flexible
- Open-source option available
Cons
- Complex setup
- Requires operational expertise
Platforms / Deployment
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports encryption, RBAC, audit logs; certifications not publicly stated.
Integrations & Ecosystem
- Kubernetes
- AWS, Azure, GCP
- CI/CD tools
Support & Community
Strong open-source community and enterprise support.
#5 — IBM Key Protect
Short description: IBM’s cloud-based KMS designed for secure key lifecycle management.
Key Features
- Root key management
- Integration with IBM Cloud
- Lifecycle control
- Access policies
- Audit logging
Pros
- Strong enterprise focus
- Reliable infrastructure
Cons
- Limited adoption outside IBM Cloud
- Smaller ecosystem
Platforms / Deployment
Cloud
Security & Compliance
Encryption, audit logs; compliance details not publicly stated.
Integrations & Ecosystem
- IBM Cloud services
- Container platforms
Support & Community
Enterprise-grade support.
#6 — Thales CipherTrust Manager
Short description: A robust enterprise KMS offering centralized key management and encryption policy enforcement.
Key Features
- Centralized key control
- Data security platform integration
- Policy-based encryption
- Multi-cloud support
- Compliance reporting
Pros
- Strong compliance capabilities
- Enterprise-grade security
Cons
- Complex deployment
- Higher cost
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Strong compliance focus; exact certifications not publicly stated.
Integrations & Ecosystem
- Cloud platforms
- Databases
- Enterprise systems
Support & Community
Enterprise support available.
#7 — Fortanix DSM
Short description: A data security manager combining KMS, secrets management, and HSM capabilities.
Key Features
- Unified security platform
- Hardware-backed encryption
- Key lifecycle management
- Multi-cloud support
- DevOps integration
Pros
- All-in-one solution
- Strong security architecture
Cons
- Premium pricing
- Learning curve
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Encryption, HSM support; certifications not publicly stated.
Integrations & Ecosystem
- Kubernetes
- Cloud providers
- DevOps tools
Support & Community
Enterprise-level support.
#8 — Oracle Cloud Infrastructure KMS
Short description: Oracle’s native KMS for securing data in Oracle Cloud environments.
Key Features
- Key lifecycle management
- HSM-backed keys
- Integration with OCI services
- Policy-based access
- Audit logging
Pros
- Strong Oracle ecosystem
- Reliable performance
Cons
- Limited outside OCI
- Smaller community
Platforms / Deployment
Cloud
Security & Compliance
Encryption, audit logs; certifications not publicly stated.
Integrations & Ecosystem
- Oracle databases
- OCI services
Support & Community
Enterprise support.
#9 — DigiCert Key Management
Short description: A platform focused on certificate lifecycle and key management.
Key Features
- Certificate management
- Key lifecycle tracking
- Automation tools
- Security monitoring
- Compliance support
Pros
- Strong certificate management
- Trusted brand
Cons
- Less focus on general KMS
- Limited cloud integrations
Platforms / Deployment
Cloud
Security & Compliance
Encryption and audit features; compliance not publicly stated.
Integrations & Ecosystem
- Certificate systems
- Enterprise IT tools
Support & Community
Good enterprise support.
#10 — Entrust KeyControl
Short description: A centralized KMS for managing encryption keys across hybrid environments.
Key Features
- Central key management
- Policy-based control
- Multi-cloud support
- Audit logging
- Data encryption integration
Pros
- Strong hybrid support
- Mature enterprise solution
Cons
- Complex setup
- Cost considerations
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Encryption, RBAC, audit logs; certifications not publicly stated.
Integrations & Ecosystem
- Cloud platforms
- Databases
- Enterprise apps
Support & Community
Enterprise support available.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| AWS KMS | AWS users | Web | Cloud | Deep AWS integration | N/A |
| Azure Key Vault | Microsoft ecosystem | Web | Cloud | Secret + key management | N/A |
| Google Cloud KMS | GCP workloads | Web | Cloud | Developer-friendly APIs | N/A |
| HashiCorp Vault | Multi-cloud | Web/Linux | Hybrid | Dynamic secrets | N/A |
| IBM Key Protect | IBM Cloud users | Web | Cloud | Enterprise lifecycle control | N/A |
| Thales CipherTrust | Enterprises | Web | Hybrid | Compliance focus | N/A |
| Fortanix DSM | DevSecOps teams | Web | Hybrid | HSM + KMS unified | N/A |
| Oracle OCI KMS | Oracle users | Web | Cloud | OCI integration | N/A |
| DigiCert KMS | Certificate mgmt | Web | Cloud | PKI focus | N/A |
| Entrust KeyControl | Hybrid infra | Web | Hybrid | Centralized control | N/A |
Evaluation & Scoring of Key Management Systems (KMS)
| Tool Name | Core | Ease | Integrations | Security | Performance | Support | Value | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| AWS KMS | 9 | 8 | 9 | 9 | 9 | 8 | 8 | 8.7 |
| Azure Key Vault | 9 | 7 | 9 | 9 | 8 | 8 | 8 | 8.5 |
| Google Cloud KMS | 8 | 8 | 8 | 9 | 9 | 8 | 8 | 8.4 |
| HashiCorp Vault | 10 | 6 | 10 | 9 | 8 | 9 | 7 | 8.6 |
| IBM Key Protect | 8 | 7 | 7 | 9 | 8 | 8 | 7 | 7.8 |
| Thales CipherTrust | 9 | 6 | 8 | 10 | 8 | 8 | 7 | 8.3 |
| Fortanix DSM | 9 | 7 | 8 | 9 | 8 | 8 | 7 | 8.2 |
| Oracle OCI KMS | 8 | 7 | 7 | 9 | 8 | 7 | 7 | 7.7 |
| DigiCert KMS | 7 | 8 | 6 | 8 | 7 | 7 | 7 | 7.2 |
| Entrust KeyControl | 9 | 6 | 8 | 9 | 8 | 8 | 7 | 8.1 |
How to interpret:
Scores are comparative and based on feature depth, usability, and ecosystem strength. Higher scores indicate stronger overall capability, but the “best” tool depends on your environment and use case.
Which Key Management Systems (KMS) Is Right for You?
Solo / Freelancer
Use cloud-native KMS like AWS, Azure, or GCP for simplicity.
SMB
Choose managed services with easy setup—AWS KMS or Azure Key Vault.
Mid-Market
HashiCorp Vault offers flexibility for growing infrastructure.
Enterprise
Thales, Entrust, or Fortanix provide advanced compliance and control.
Budget vs Premium
- Budget: Cloud-native tools
- Premium: Enterprise platforms with compliance
Feature Depth vs Ease of Use
- Easy: AWS KMS
- Advanced: Vault or Thales
Integrations & Scalability
- Multi-cloud: Vault, Fortanix
- Single cloud: AWS/Azure/GCP
Security & Compliance Needs
- High compliance: Thales, Entrust
- Standard: AWS, Azure
Frequently Asked Questions (FAQs)
What is a Key Management System?
A system that securely manages encryption keys used to protect data.
Why is KMS important?
It ensures secure encryption and compliance with data protection regulations.
Is KMS only for enterprises?
No, SMBs also benefit from cloud-managed KMS solutions.
Can KMS integrate with DevOps tools?
Yes, most modern KMS tools support CI/CD integrations.
What is key rotation?
Automatically replacing encryption keys to improve security.
Is KMS the same as secrets management?
Not exactly, but many tools combine both features.
What deployment options exist?
Cloud, self-hosted, and hybrid.
Are KMS tools expensive?
Varies; cloud KMS can be cost-effective, enterprise tools are premium.
Can I use multiple KMS tools?
Yes, especially in multi-cloud environments.
What are common mistakes?
Poor access control, lack of rotation, and weak audit monitoring.
Conclusion
Key Management Systems are no longer optional—they are a core part of modern security architecture. Whether you are running cloud-native applications, handling financial data, or building secure DevOps pipelines, the ability to manage encryption keys effectively directly impacts your security posture. There is no single “best” KMS for every organization. Cloud-native tools like AWS KMS, Azure Key Vault, and Google Cloud KMS are ideal for simplicity and scalability within their ecosystems. Meanwhile, solutions like HashiCorp Vault, Thales CipherTrust, and Fortanix DSM provide greater flexibility and enterprise-grade control for multi-cloud or compliance-heavy environment