Introduction
Database Security Tools are systems designed to protect databases from unauthorized access, data breaches, misuse, and internal threats. They combine monitoring, encryption, access control, and auditing to ensure that sensitive data remains secure across environments.
In modern cloud and AI-driven architectures, databases are accessed by applications, APIs, and users from multiple locations. This increases the risk of exposure, making database security tools a critical layer in any organization’s security strategy. Whether it’s financial records, healthcare data, or customer information, protecting databases is no longer optional—it’s essential.
Real-world use cases include:
- Securing customer data in SaaS platforms
- Monitoring insider threats and suspicious queries
- Protecting cloud databases and data warehouses
- Ensuring compliance with regulatory requirements
- Detecting vulnerabilities and misconfigurations
What buyers should evaluate:
- Data discovery and classification capabilities
- Real-time monitoring and alerting
- Access control and identity integration
- Encryption, masking, and tokenization features
- Compliance reporting and audit trails
- Integration with cloud and DevOps tools
- Scalability across hybrid environments
- Ease of deployment and management
Best for: Security teams, DBAs, DevOps engineers, SaaS companies, fintech, healthcare, and enterprises managing sensitive data.
Not ideal for: Small-scale projects with minimal data sensitivity where basic database permissions and encryption are sufficient.
Key Trends in Database Security Tools
- AI-driven data discovery: Automatically identifying sensitive data across databases
- Zero Trust data access: Identity-based access replacing network-based security
- Agentless deployment models: Faster setup with minimal performance impact
- Real-time anomaly detection: Immediate alerts for unusual database behavior
- Cloud-native security platforms: Designed for AWS, Azure, and GCP environments
- Data masking and tokenization: Protecting sensitive fields dynamically
- Compliance automation: Built-in reporting for regulatory requirements
- DevOps integration: Security embedded into CI/CD pipelines
- Unified data security platforms: Combining multiple data protection layers
- Policy-based access control: Fine-grained control over data access
How We Selected These Tools (Methodology)
- Evaluated market adoption and enterprise usage
- Assessed core database security features and capabilities
- Reviewed real-time monitoring and threat detection strength
- Compared integration with cloud and DevOps ecosystems
- Analyzed security posture and compliance readiness
- Considered performance impact and scalability
- Evaluated ease of deployment and usability
- Reviewed fit across SMB, mid-market, and enterprise users
- Considered vendor maturity and support ecosystem
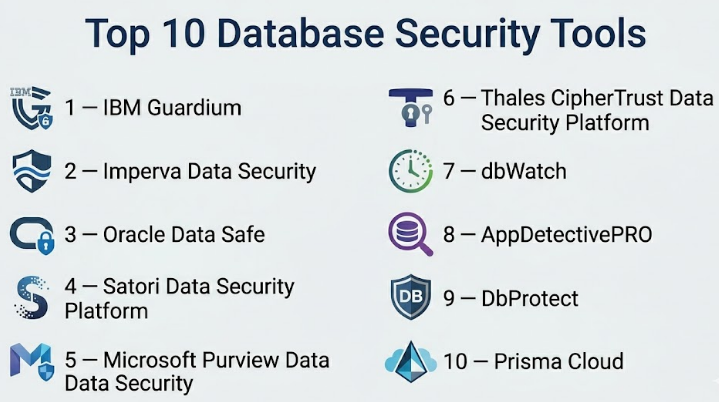
Top 10 Database Security Tools
#1 — IBM Guardium
Short description (2–3 lines): An enterprise-grade database security platform providing real-time monitoring, data protection, and compliance management across hybrid environments.
Key Features
- Real-time database activity monitoring
- Data discovery and classification
- Vulnerability assessment
- Encryption and masking
- Compliance reporting
- Threat detection
Pros
- Strong enterprise capabilities
- Comprehensive compliance features
Cons
- Complex deployment
- Higher cost
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Encryption, RBAC, audit logs; certifications not publicly stated
Integrations & Ecosystem
Supports enterprise integrations:
- SIEM tools
- Cloud platforms
- Multiple database systems
Support & Community
Enterprise-level support with strong documentation.
#2 — Imperva Data Security
Short description: A widely adopted platform focused on database monitoring, threat detection, and compliance management.
Key Features
- Database activity monitoring
- Threat intelligence integration
- Data masking
- Compliance reporting
- Risk assessment
Pros
- Strong threat detection
- User-friendly interface
Cons
- Premium pricing
- Limited customization options
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Encryption, audit logs; compliance details not publicly stated
Integrations & Ecosystem
- Cloud platforms
- Security systems
- Database environments
Support & Community
Reliable enterprise support.
#3 — Oracle Data Safe
Short description: A cloud-based database security service designed for Oracle environments with automation and risk analysis capabilities.
Key Features
- Data discovery
- User risk assessment
- Activity auditing
- Data masking
- Security configuration analysis
Pros
- Strong Oracle integration
- Easy cloud deployment
Cons
- Limited multi-cloud support
- Vendor dependency
Platforms / Deployment
Cloud
Security & Compliance
Encryption, audit logs; certifications not publicly stated
Integrations & Ecosystem
- Oracle databases
- Cloud infrastructure
Support & Community
Strong vendor support.
#4 — Satori Data Security Platform
Short description: A modern platform focusing on controlling and monitoring data access across cloud databases.
Key Features
- Data access governance
- Real-time monitoring
- Policy enforcement
- Data discovery
- Activity auditing
Pros
- Easy deployment
- Strong cloud compatibility
Cons
- Limited support for legacy systems
- Smaller ecosystem
Platforms / Deployment
Cloud
Security & Compliance
Access control, audit logs; certifications not publicly stated
Integrations & Ecosystem
- Cloud providers
- Identity systems
- Data platforms
Support & Community
Growing documentation and support ecosystem.
#5 — Microsoft Purview Data Security
Short description: A unified data governance and security platform for managing and protecting data across Microsoft ecosystems.
Key Features
- Data discovery and classification
- Data lineage tracking
- Policy enforcement
- Risk management
- Compliance support
Pros
- Strong Microsoft integration
- Unified governance approach
Cons
- Learning curve
- Best suited for Microsoft environments
Platforms / Deployment
Cloud
Security & Compliance
RBAC, audit logs; certifications not publicly stated
Integrations & Ecosystem
- Azure
- Microsoft ecosystem tools
- Analytics platforms
Support & Community
Strong enterprise support.
#6 — Thales CipherTrust Data Security Platform
Short description: A data-centric security platform offering encryption, key management, and database protection capabilities.
Key Features
- Encryption and tokenization
- Centralized policy management
- Data masking
- Compliance reporting
- Multi-cloud support
Pros
- Strong encryption capabilities
- Enterprise-grade security
Cons
- Complex deployment
- Higher cost
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Encryption, RBAC; certifications not publicly stated
Integrations & Ecosystem
- Cloud platforms
- Databases
- Enterprise applications
Support & Community
Enterprise-level support available.
#7 — dbWatch
Short description: A database monitoring tool with security insights, focusing on performance and operational visibility.
Key Features
- Database monitoring
- Real-time alerts
- Performance tracking
- Resource utilization insights
- Multi-database support
Pros
- Easy to use
- Strong monitoring features
Cons
- Limited advanced security features
- Less focus on compliance
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- SQL databases
- Monitoring tools
- Infrastructure platforms
Support & Community
Moderate support ecosystem.
#8 — AppDetectivePRO
Short description: A vulnerability assessment tool designed to identify risks and compliance issues in databases.
Key Features
- Vulnerability scanning
- Compliance checks
- Risk assessment
- Reporting tools
- Policy management
Pros
- Strong compliance reporting
- Easy-to-understand insights
Cons
- Limited real-time monitoring
- Not a full security platform
Platforms / Deployment
Self-hosted
Security & Compliance
Supports compliance frameworks; details not publicly stated
Integrations & Ecosystem
- Database systems
- Security tools
Support & Community
Enterprise support available.
#9 — DbProtect
Short description: A database security tool focused on vulnerability assessment and compliance management.
Key Features
- Vulnerability assessment
- Compliance auditing
- Risk analysis
- Policy enforcement
- Reporting
Pros
- Strong compliance capabilities
- Customizable policies
Cons
- Limited monitoring features
- Complex setup
Platforms / Deployment
Self-hosted
Security & Compliance
Supports compliance standards; details not publicly stated
Integrations & Ecosystem
- Databases
- Security platforms
Support & Community
Enterprise support available.
#10 — Prisma Cloud (Database Security)
Short description: A cloud-native security platform providing database protection, vulnerability detection, and compliance monitoring.
Key Features
- Cloud database security
- Vulnerability scanning
- Risk detection
- Compliance monitoring
- Policy enforcement
Pros
- Strong cloud integration
- Advanced threat detection
Cons
- Complex setup
- Premium pricing
Platforms / Deployment
Cloud
Security & Compliance
Encryption, monitoring; certifications not publicly stated
Integrations & Ecosystem
- Cloud providers
- DevOps tools
- Security platforms
Support & Community
Strong enterprise support.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| IBM Guardium | Enterprise | Web | Hybrid | Real-time monitoring | N/A |
| Imperva | Security teams | Web | Hybrid | Threat detection | N/A |
| Oracle Data Safe | Oracle users | Web | Cloud | Oracle integration | N/A |
| Satori | Cloud teams | Web | Cloud | Access control automation | N/A |
| Microsoft Purview | Microsoft users | Web | Cloud | Data governance | N/A |
| Thales CipherTrust | Enterprises | Web | Hybrid | Encryption platform | N/A |
| dbWatch | Monitoring | Web | Hybrid | Performance insights | N/A |
| AppDetectivePRO | Compliance | Web | Self-hosted | Vulnerability scanning | N/A |
| DbProtect | Compliance | Web | Self-hosted | Policy enforcement | N/A |
| Prisma Cloud | Cloud security | Web | Cloud | Cloud-native protection | N/A |
Evaluation & Scoring of Database Security Tools
| Tool Name | Core | Ease | Integrations | Security | Performance | Support | Value | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| IBM Guardium | 10 | 7 | 9 | 10 | 9 | 9 | 7 | 9.0 |
| Imperva | 9 | 8 | 8 | 9 | 8 | 8 | 7 | 8.4 |
| Oracle Data Safe | 8 | 8 | 7 | 9 | 8 | 8 | 7 | 8.0 |
| Satori | 8 | 9 | 8 | 8 | 8 | 7 | 8 | 8.1 |
| Microsoft Purview | 9 | 7 | 9 | 9 | 8 | 8 | 7 | 8.5 |
| Thales CipherTrust | 9 | 6 | 8 | 10 | 8 | 8 | 7 | 8.4 |
| dbWatch | 7 | 8 | 7 | 7 | 8 | 7 | 8 | 7.5 |
| AppDetectivePRO | 7 | 7 | 6 | 8 | 7 | 7 | 8 | 7.3 |
| DbProtect | 7 | 6 | 6 | 8 | 7 | 7 | 7 | 7.0 |
| Prisma Cloud | 9 | 7 | 9 | 9 | 8 | 8 | 7 | 8.5 |
How to interpret the scores:
These scores are relative and help compare tools based on feature strength, usability, and ecosystem support. Enterprise tools tend to score higher in security and compliance, while lightweight tools score better in ease of use and cost efficiency. The right choice depends on your specific use case rather than the highest score alone.
Which Database Security Tools Is Right for You?
Solo / Freelancer
Choose simple monitoring or lightweight tools that are easy to deploy and maintain.
SMB
Look for tools like Imperva or Satori that balance ease of use with strong security features.
Mid-Market
Consider platforms like Microsoft Purview or Oracle Data Safe for better governance and scalability.
Enterprise
Go for IBM Guardium, Thales CipherTrust, or Prisma Cloud for advanced security and compliance.
Budget vs Premium
- Budget-friendly: dbWatch, AppDetectivePRO
- Premium: IBM Guardium, Prisma Cloud
Feature Depth vs Ease of Use
- Easy to use: Satori, Imperva
- Feature-rich: Guardium, Thales
Integrations & Scalability
- Multi-cloud: Prisma Cloud, Satori
- Ecosystem-specific: Oracle Data Safe, Microsoft Purview
Security & Compliance Needs
- High compliance: Guardium, Thales
- Standard security: Imperva, Satori
Frequently Asked Questions (FAQs)
What are Database Security Tools?
They are tools designed to protect databases from unauthorized access, breaches, and misuse.
Why are database security tools important?
They help prevent data leaks, ensure compliance, and detect suspicious activity.
Are these tools only for large enterprises?
No, many tools are suitable for SMBs and growing organizations.
Can database security tools integrate with cloud platforms?
Yes, most modern tools support cloud integrations.
What is data masking?
It hides sensitive data while keeping it usable for testing or analytics.
Do these tools impact database performance?
Some tools may add overhead, but modern solutions minimize performance impact.
What is real-time monitoring?
It tracks database activity continuously and alerts on suspicious behavior.
Are database security tools expensive?
Pricing varies depending on features and scale.
Can these tools help with compliance?
Yes, many tools provide audit logs and reporting for compliance.
What are common mistakes when implementing database security?
Ignoring monitoring, weak access control, and not updating security policies.
Conclusion
Database security tools have become a fundamental part of modern data protection strategies. As organizations handle increasing volumes of sensitive data across cloud and hybrid environments, the need for visibility, control, and automation in database security is critical. There is no one-size-fits-all solution. Enterprise platforms like IBM Guardium and Thales CipherTrust offer deep control and compliance capabilities, while tools like Satori and Imperva provide a balance of usability and security. Lightweight tools are suitable for smaller environments, while cloud-native solutions are ideal for scalable architectures.