Introduction
Network Detection & Response (NDR) is a cybersecurity solution focused on monitoring network traffic to detect, analyze, and respond to threats in real time. Unlike endpoint-based tools, NDR operates at the network level, providing visibility into east-west traffic, lateral movement, and hidden threats that may bypass endpoint defenses.
Modern organizations face increasingly sophisticated attacks that often move silently across networks. NDR platforms help security teams identify anomalies, detect advanced threats, and respond quickly using behavioral analytics, machine learning, and deep packet inspection.
Common Use Cases
- Detecting lateral movement inside networks
- Identifying advanced persistent threats (APTs)
- Monitoring encrypted traffic for anomalies
- Enhancing SOC visibility across network layers
- Investigating suspicious network behavior
What Buyers Should Evaluate
- Network visibility and traffic analysis depth
- AI/ML-based anomaly detection capabilities
- Integration with SIEM, EDR, and XDR tools
- Deployment model (cloud, on-prem, hybrid)
- Scalability across distributed environments
- Ease of investigation and alerting
- Encryption traffic analysis capabilities
- Performance and network impact
- Threat intelligence integration
- Pricing and licensing model
Best for: Security teams, SOC analysts, enterprises, and organizations with complex or distributed networks.
Not ideal for: Small businesses with simple networks or those relying solely on endpoint-based security tools.
Key Trends in Network Detection & Response (NDR)
- AI-driven anomaly detection: Behavioral analysis replacing signature-based detection
- Encrypted traffic analysis: Detecting threats without decrypting data
- Integration with XDR platforms: Unified threat detection across endpoints, network, and cloud
- Cloud-native NDR solutions: Scalable and easier to deploy
- Automated response workflows: Faster threat containment
- Deep packet inspection advancements: Improved visibility into network traffic
- Threat hunting capabilities: Proactive identification of hidden threats
- Zero Trust alignment: Continuous monitoring of network behavior
- API-first platforms: Integration with modern security stacks
- Managed NDR services: Outsourced detection and response
How We Selected These Tools (Methodology)
- Evaluated market presence and adoption
- Assessed depth of network visibility and analytics
- Reviewed threat detection accuracy and innovation
- Considered ease of deployment and usability
- Analyzed integration capabilities with security ecosystems
- Examined performance and scalability
- Included a mix of enterprise and mid-market solutions
- Factored in support quality and ecosystem maturity
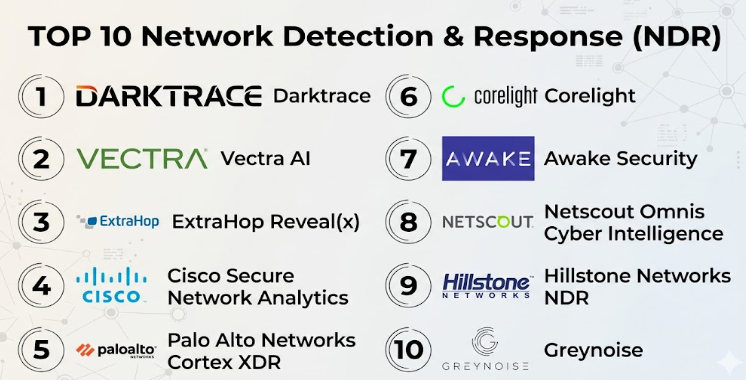
Top Network Detection & Response (NDR)
#1 — Darktrace
Short description: AI-driven NDR platform focused on autonomous threat detection and response.
Key Features
- Self-learning AI models
- Real-time anomaly detection
- Autonomous response capabilities
- Network traffic analysis
- Threat visualization dashboards
Pros
- Strong AI-based detection
- Automated response capabilities
Cons
- Premium pricing
- Requires tuning for optimal results
Platforms / Deployment
Cloud / On-prem / Hybrid
Security & Compliance
Encryption, audit logs
Compliance varies
Integrations & Ecosystem
Integrates with security tools and APIs
- SIEM platforms
- Cloud tools
- Security stacks
Support & Community
Enterprise-level support
#2 — Vectra AI
Short description: NDR platform specializing in AI-driven threat detection across hybrid environments.
Key Features
- AI-based threat detection
- Behavioral analytics
- Threat prioritization
- Network visibility
- Cloud and SaaS monitoring
Pros
- Strong detection accuracy
- Good threat prioritization
Cons
- Complex setup
- Higher cost
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Encryption
Compliance varies
Integrations & Ecosystem
Integrates with SIEM and cloud platforms
Support & Community
Strong enterprise support
#3 — ExtraHop Reveal(x)
Short description: NDR solution providing deep network visibility and real-time analytics.
Key Features
- Real-time network analytics
- Threat detection
- Performance monitoring
- Encrypted traffic analysis
- Forensic investigation tools
Pros
- Strong visibility
- Good analytics capabilities
Cons
- Expensive
- Requires expertise
Platforms / Deployment
Cloud / On-prem
Security & Compliance
Encryption, audit logs
Compliance varies
Integrations & Ecosystem
Integrates with enterprise security tools
Support & Community
Enterprise support
#4 — Cisco Secure Network Analytics
Short description: NDR solution focused on network visibility and threat detection.
Key Features
- Network traffic analysis
- Threat detection
- Behavioral analytics
- Incident response
- Scalable architecture
Pros
- Strong enterprise integration
- Reliable performance
Cons
- Complex deployment
- Requires Cisco ecosystem knowledge
Platforms / Deployment
On-prem / Hybrid
Security & Compliance
Encryption
Compliance varies
Integrations & Ecosystem
Deep Cisco integrations
Support & Community
Enterprise support
#5 — Palo Alto Networks Cortex XDR (NDR Capabilities)
Short description: Unified detection platform with strong network detection capabilities.
Key Features
- Network traffic analysis
- Behavioral analytics
- Threat detection
- Cross-data correlation
- Incident response
Pros
- Unified security platform
- Strong analytics
Cons
- Complex setup
- Premium pricing
Platforms / Deployment
Cloud
Security & Compliance
MFA, encryption
Compliance varies
Integrations & Ecosystem
Integrates with Palo Alto ecosystem
Support & Community
Enterprise support
#6 — Corelight
Short description: Open-network detection platform based on Zeek for deep network visibility.
Key Features
- Network traffic analysis
- Threat detection
- Zeek-based analytics
- Open architecture
- High-fidelity data
Pros
- Open and flexible
- Strong visibility
Cons
- Requires expertise
- Setup complexity
Platforms / Deployment
On-prem / Cloud
Security & Compliance
Encryption
Compliance varies
Integrations & Ecosystem
Integrates with SIEM and open-source tools
Support & Community
Strong technical community
#7 — Awake Security (Arista NDR)
Short description: NDR platform focusing on AI-driven network threat detection.
Key Features
- AI-driven analytics
- Network visibility
- Threat detection
- Behavioral monitoring
- Incident response
Pros
- Strong AI capabilities
- Good detection accuracy
Cons
- Limited public info
- Enterprise-focused
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Integrates with enterprise tools
Support & Community
Varies / Not publicly stated
#8 — Netscout Omnis Cyber Intelligence
Short description: NDR solution focusing on network performance and security visibility.
Key Features
- Network visibility
- Threat detection
- Traffic analysis
- Performance monitoring
- Incident investigation
Pros
- Strong network analytics
- Reliable performance
Cons
- Complex interface
- High cost
Platforms / Deployment
On-prem / Hybrid
Security & Compliance
Encryption
Compliance varies
Integrations & Ecosystem
Integrates with network and security tools
Support & Community
Enterprise support
#9 — Hillstone Networks NDR
Short description: Network detection solution with integrated threat intelligence.
Key Features
- Threat detection
- Network monitoring
- Behavioral analytics
- Incident response
- Threat intelligence
Pros
- Cost-effective
- Integrated features
Cons
- Smaller ecosystem
- Limited global presence
Platforms / Deployment
On-prem / Cloud
Security & Compliance
Encryption
Compliance varies
Integrations & Ecosystem
Basic integrations
Support & Community
Moderate support
#10 — Greynoise (Network Intelligence)
Short description: Network intelligence platform focused on filtering noise and identifying threats.
Key Features
- Threat intelligence
- Noise filtering
- IP reputation analysis
- Network visibility
- Analytics tools
Pros
- Unique intelligence capabilities
- Reduces alert noise
Cons
- Not a full standalone NDR
- Limited response features
Platforms / Deployment
Cloud
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Integrates with SIEM and security tools
Support & Community
Growing community
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Darktrace | AI-driven detection | Web | Cloud/Hybrid | Autonomous response | N/A |
| Vectra AI | Threat detection | Web | Cloud/Hybrid | Behavioral analytics | N/A |
| ExtraHop | Network visibility | Web | Cloud/On-prem | Real-time analytics | N/A |
| Cisco Secure Network Analytics | Enterprises | Web | Hybrid | Network telemetry | N/A |
| Cortex XDR | Unified detection | Web | Cloud | Cross-data analytics | N/A |
| Corelight | Open architecture | Web | Hybrid | Zeek-based analytics | N/A |
| Awake Security | AI detection | Web | Hybrid | Behavioral monitoring | N/A |
| Netscout Omnis | Performance + security | Web | Hybrid | Traffic analytics | N/A |
| Hillstone | SMB/enterprise | Web | Hybrid | Integrated intelligence | N/A |
| Greynoise | Threat intelligence | Web | Cloud | Noise filtering | N/A |
Network Detection & Response (NDR)
Scoring Table
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Darktrace | 9 | 7 | 8 | 9 | 9 | 8 | 6 | 8.3 |
| Vectra AI | 9 | 7 | 8 | 9 | 9 | 8 | 6 | 8.3 |
| ExtraHop | 9 | 6 | 8 | 9 | 9 | 8 | 6 | 8.1 |
| Cisco | 8 | 6 | 9 | 9 | 9 | 8 | 6 | 8.0 |
| Cortex XDR | 9 | 6 | 9 | 9 | 8 | 7 | 6 | 8.1 |
| Corelight | 8 | 5 | 9 | 8 | 8 | 7 | 8 | 7.9 |
| Awake Security | 8 | 6 | 7 | 8 | 8 | 7 | 6 | 7.5 |
| Netscout | 8 | 6 | 7 | 8 | 9 | 7 | 6 | 7.7 |
| Hillstone | 7 | 7 | 6 | 7 | 8 | 7 | 8 | 7.4 |
| Greynoise | 7 | 8 | 7 | 7 | 7 | 6 | 8 | 7.3 |
How to interpret scores:
- Higher scores indicate stronger overall capabilities
- Enterprise tools excel in core features and security
- Simpler tools perform better in ease and value
- Choose based on network complexity and team expertise
Which Network Detection & Response (NDR) Is Right for You?
Solo / Freelancer
- NDR is generally not required
- Consider basic network monitoring tools instead
SMB
- Hillstone or Corelight
- Balance cost and functionality
Mid-Market
- ExtraHop or Vectra AI
- Strong visibility and detection
Enterprise
- Darktrace, Cisco, Cortex XDR
- Advanced analytics and scalability
Budget vs Premium
- Budget: Hillstone, Corelight
- Premium: Darktrace, Vectra
Feature Depth vs Ease of Use
- Feature-rich: Darktrace, ExtraHop
- Easier: Hillstone, Greynoise
Integrations & Scalability
- Enterprise ecosystems: Cisco, Palo Alto
- Open ecosystem: Corelight
Security & Compliance Needs
- High: Darktrace, Cisco
- Moderate: Hillstone, Corelight
Network Detection & Response (NDR)
What is NDR?
NDR monitors network traffic to detect and respond to threats.
How is NDR different from EDR?
NDR focuses on network traffic, while EDR focuses on endpoints.
Is NDR necessary for small businesses?
Usually not, unless network complexity is high.
How is NDR priced?
Typically based on network traffic volume or deployment size.
Can NDR detect encrypted threats?
Yes, using behavioral analysis.
What is lateral movement detection?
Identifying attackers moving within a network.
Can NDR integrate with SIEM?
Yes, most tools support SIEM integration.
How complex is deployment?
Varies from moderate to complex.
What are common mistakes?
Ignoring alerts, poor configuration, lack of integration.
Is cloud-based NDR better?
Cloud NDR offers scalability and easier management.
Conclusion
Network Detection & Response (NDR) platforms provide critical visibility into network activity, enabling organizations to detect sophisticated threats that traditional endpoint or perimeter defenses may miss. Solutions like Darktrace and Vectra AI excel in AI-driven detection, while platforms such as ExtraHop and Cisco offer deep network analytics and enterprise-grade scalability. However, the right choice depends on your network complexity, security maturity, and existing infrastructure. Instead of selecting a tool based solely on features, organizations should focus on how well it integrates with their broader security stack, supports their investigation workflows, and scales with network growth. A practical approach is to shortlist a few solutions, run controlled evaluations, and validate real-world detection accuracy and usability before making a long-term investment.