Introduction
Endpoint Detection & Response (EDR) is a cybersecurity solution focused on detecting, investigating, and responding to threats on endpoints such as laptops, servers, and mobile devices. Unlike traditional antivirus or even EPP, EDR provides continuous monitoring, deep visibility, and real-time response capabilities to identify advanced threats that bypass prevention layers.
With the rise of sophisticated cyberattacks, ransomware, and insider threats, organizations need more than just prevention—they need visibility and rapid response. EDR platforms enable security teams to analyze incidents, trace attack paths, and automate remediation.
Common Use Cases
- Investigating suspicious endpoint activity
- Responding to ransomware or malware incidents
- Monitoring user behavior for insider threats
- Conducting forensic analysis after a breach
- Enhancing SOC (Security Operations Center) capabilities
What Buyers Should Evaluate
- Threat detection accuracy and behavioral analytics
- Real-time response and automation capabilities
- Endpoint visibility and telemetry depth
- Integration with SIEM, XDR, and SOAR tools
- Ease of use and alert fatigue management
- Scalability across endpoints
- Performance impact on devices
- Incident investigation tools
- Reporting and compliance capabilities
- Pricing and licensing model
Best for: Security teams, SOC analysts, enterprises, and organizations with high cybersecurity risk or compliance needs.
Not ideal for: Very small teams without dedicated security expertise or organizations that only need basic antivirus protection.
Key Trends in Endpoint Detection & Response (EDR)
- AI-driven threat detection: Behavioral analysis for detecting unknown threats
- Automation in response workflows: Faster containment and remediation
- Integration with XDR platforms: Unified visibility across security layers
- Threat hunting capabilities: Proactive detection of hidden threats
- Cloud-native EDR solutions: Scalable and easier to manage
- Reduced alert fatigue: Smarter prioritization using analytics
- Forensic data collection: Deep endpoint telemetry for investigations
- Zero Trust integration: Continuous validation of endpoint behavior
- Managed EDR services (MDR): Outsourced monitoring and response
- API-driven ecosystems: Integration with modern security stacks
How We Selected These Tools (Methodology)
- Evaluated market adoption and leadership
- Assessed depth of detection and response capabilities
- Reviewed incident investigation and threat hunting features
- Considered ease of use and SOC efficiency improvements
- Analyzed integration capabilities with security ecosystems
- Examined performance and scalability across endpoints
- Included a mix of enterprise-grade and mid-market solutions
- Factored in support quality and community presence
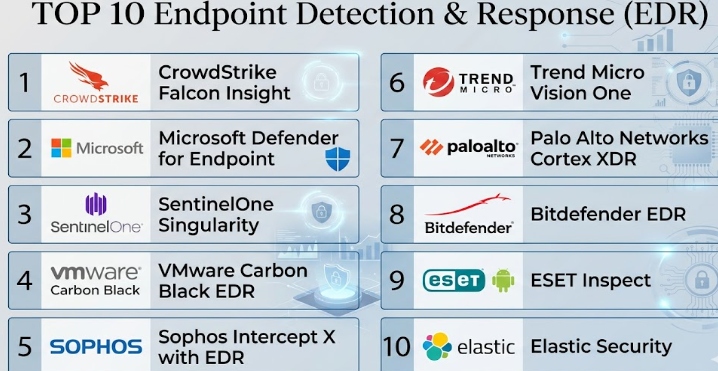
Top Endpoint Detection & Response (EDR)
#1 — CrowdStrike Falcon Insight
Short description: A leading cloud-native EDR platform offering advanced threat detection, investigation, and response capabilities.
Key Features
- Real-time endpoint monitoring
- AI-driven threat detection
- Threat hunting capabilities
- Incident response automation
- Cloud-native architecture
- Detailed forensic data collection
Pros
- Excellent visibility and detection accuracy
- Lightweight agent
Cons
- Premium pricing
- Requires skilled security teams
Platforms / Deployment
Windows / macOS / Linux / Cloud
Security & Compliance
MFA, encryption, audit logs
Compliance varies
Integrations & Ecosystem
Strong ecosystem with APIs and integrations
- SIEM tools
- Threat intelligence platforms
- Cloud services
Support & Community
Enterprise-grade support and strong documentation
#2 — Microsoft Defender for Endpoint
Short description: Integrated EDR solution within the Microsoft security ecosystem.
Key Features
- Endpoint detection and response
- Automated investigation
- Threat intelligence integration
- Vulnerability management
- Behavioral analytics
Pros
- Seamless Microsoft integration
- Strong automation features
Cons
- Best suited for Microsoft environments
- Complex configuration
Platforms / Deployment
Windows / macOS / Linux / Cloud
Security & Compliance
MFA, RBAC, audit logs
Compliance varies
Integrations & Ecosystem
Deep Microsoft integrations
- Azure
- Microsoft 365
- Security tools
Support & Community
Strong enterprise support
#3 — SentinelOne Singularity
Short description: Autonomous EDR platform focused on AI-powered detection and response.
Key Features
- AI-based threat detection
- Automated response
- Ransomware rollback
- Endpoint visibility
- Behavioral monitoring
Pros
- Strong automation
- Fast response capabilities
Cons
- Higher cost
- Learning curve
Platforms / Deployment
Windows / macOS / Linux / Cloud
Security & Compliance
MFA, encryption
Compliance varies
Integrations & Ecosystem
Integrates with SIEM and XDR tools
Support & Community
Good enterprise support
#4 — VMware Carbon Black EDR
Short description: Cloud-native EDR platform focused on threat hunting and endpoint visibility.
Key Features
- Endpoint telemetry
- Threat hunting tools
- Behavioral analytics
- Incident response workflows
- Cloud-native deployment
Pros
- Strong threat visibility
- Good for advanced security teams
Cons
- Complex setup
- Higher cost
Platforms / Deployment
Windows / macOS / Linux / Cloud
Security & Compliance
MFA, encryption
Compliance varies
Integrations & Ecosystem
Integrates with VMware ecosystem and SIEM tools
Support & Community
Enterprise support
#5 — Sophos Intercept X with EDR
Short description: EDR solution combining endpoint protection with detection and response capabilities.
Key Features
- Threat detection and response
- Root cause analysis
- Ransomware protection
- Endpoint monitoring
- Managed threat response
Pros
- Easy to use
- Strong ransomware protection
Cons
- Limited advanced customization
- Performance impact on older devices
Platforms / Deployment
Windows / macOS / Linux / Cloud
Security & Compliance
Encryption, MFA
Compliance varies
Integrations & Ecosystem
Integrates with Sophos ecosystem
Support & Community
Strong support
#6 — Trend Micro Vision One (EDR/XDR)
Short description: EDR solution integrated into a broader XDR platform.
Key Features
- Endpoint detection and response
- Threat intelligence
- Behavioral analytics
- Incident investigation tools
- Cross-layer visibility
Pros
- Strong threat intelligence
- Unified visibility
Cons
- Complex interface
- Requires tuning
Platforms / Deployment
Windows / macOS / Cloud
Security & Compliance
Encryption, audit logs
Compliance varies
Integrations & Ecosystem
Integrates with SIEM and cloud platforms
Support & Community
Strong support
#7 — Palo Alto Networks Cortex XDR
Short description: Advanced EDR platform with AI-driven detection and cross-data analytics.
Key Features
- Behavioral analytics
- Threat detection and response
- Automated investigations
- Cross-data correlation
- Incident management
Pros
- Strong analytics capabilities
- Good integration with Palo Alto ecosystem
Cons
- Complex deployment
- Premium pricing
Platforms / Deployment
Windows / macOS / Linux / Cloud
Security & Compliance
MFA, encryption
Compliance varies
Integrations & Ecosystem
Integrates with Palo Alto tools and APIs
Support & Community
Enterprise support
#8 — Bitdefender EDR
Short description: EDR solution focused on strong detection capabilities and analytics.
Key Features
- Threat detection
- Endpoint monitoring
- Risk analytics
- Incident investigation
- Behavioral analysis
Pros
- Strong detection rates
- Good value
Cons
- Interface complexity
- Requires tuning
Platforms / Deployment
Windows / macOS / Linux / Cloud
Security & Compliance
Encryption
Compliance varies
Integrations & Ecosystem
APIs and integrations with security tools
Support & Community
Good documentation
#9 — ESET Inspect
Short description: Lightweight EDR solution designed for SMBs and mid-sized organizations.
Key Features
- Threat detection
- Incident response
- Endpoint visibility
- Forensic analysis
- Reporting tools
Pros
- Lightweight and efficient
- Affordable
Cons
- Limited advanced features
- Smaller ecosystem
Platforms / Deployment
Windows / macOS / Linux
Security & Compliance
Encryption
Compliance varies
Integrations & Ecosystem
Basic integrations
Support & Community
Good support
#10 — Elastic Security (EDR)
Short description: Open and flexible EDR solution built on the Elastic Stack.
Key Features
- Endpoint telemetry
- Threat detection
- SIEM integration
- Threat hunting
- Open-source flexibility
Pros
- Highly customizable
- Strong analytics capabilities
Cons
- Requires expertise
- Setup complexity
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
Encryption
Compliance varies
Integrations & Ecosystem
Strong integration with Elastic ecosystem
Support & Community
Strong open-source community
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| CrowdStrike Falcon Insight | Enterprise | Windows, macOS, Linux | Cloud | AI detection | N/A |
| Microsoft Defender | Microsoft users | Windows, macOS, Linux | Cloud | Deep integration | N/A |
| SentinelOne | Automation | Windows, macOS, Linux | Cloud | Autonomous response | N/A |
| VMware Carbon Black | Threat hunting | Windows, macOS, Linux | Cloud | Endpoint telemetry | N/A |
| Sophos Intercept X | SMB & enterprise | Windows, macOS, Linux | Cloud | Ransomware defense | N/A |
| Trend Micro Vision One | XDR users | Windows, macOS | Cloud | Cross-layer visibility | N/A |
| Palo Alto Cortex XDR | Enterprises | Windows, macOS, Linux | Cloud | AI analytics | N/A |
| Bitdefender EDR | SMB & enterprise | Windows, macOS, Linux | Cloud | Risk analytics | N/A |
| ESET Inspect | SMBs | Windows, macOS, Linux | Hybrid | Lightweight agent | N/A |
| Elastic Security | Open-source users | Web | Cloud/Self-hosted | Custom analytics | N/A |
Endpoint Detection & Response (EDR)
Scoring Table
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| CrowdStrike | 10 | 8 | 9 | 10 | 9 | 9 | 7 | 9.0 |
| Microsoft Defender | 9 | 7 | 10 | 9 | 9 | 9 | 8 | 8.9 |
| SentinelOne | 9 | 7 | 8 | 9 | 9 | 8 | 7 | 8.5 |
| VMware Carbon Black | 9 | 6 | 8 | 9 | 8 | 7 | 6 | 8.0 |
| Sophos | 8 | 8 | 7 | 8 | 7 | 8 | 8 | 7.9 |
| Trend Micro | 8 | 6 | 8 | 8 | 8 | 8 | 7 | 7.8 |
| Palo Alto Cortex | 9 | 6 | 9 | 9 | 8 | 7 | 6 | 8.1 |
| Bitdefender | 8 | 7 | 7 | 8 | 8 | 7 | 9 | 7.9 |
| ESET | 7 | 8 | 6 | 7 | 8 | 7 | 9 | 7.6 |
| Elastic Security | 8 | 5 | 9 | 8 | 7 | 6 | 8 | 7.6 |
How to interpret scores:
- Scores are comparative and based on overall capabilities
- Enterprise tools score higher in core features and security
- SMB tools score better in ease of use and value
- Choose based on your operational needs and team expertise
Which Endpoint Detection & Response (EDR) Is Right for You?
Solo / Freelancer
- Elastic Security or ESET Inspect
- Cost-effective and flexible
SMB
- Sophos or Bitdefender
- Easy deployment with strong protection
Mid-Market
- Trend Micro or SentinelOne
- Balance of automation and scalability
Enterprise
- CrowdStrike, Microsoft Defender, Palo Alto Cortex XDR
- Advanced analytics and large-scale management
Budget vs Premium
- Budget: ESET, Elastic
- Premium: CrowdStrike, SentinelOne
Feature Depth vs Ease of Use
- Feature-rich: Cortex XDR, CrowdStrike
- Easy-to-use: Sophos, ESET
Integrations & Scalability
- Microsoft ecosystem: Defender
- Open ecosystem: Elastic
Security & Compliance Needs
- High compliance: CrowdStrike, Cortex XDR
- Moderate: Bitdefender, Sophos
Endpoint Detection & Response (EDR)
What is EDR?
EDR monitors endpoints continuously to detect and respond to threats.
How is EDR different from EPP?
EPP focuses on prevention, while EDR focuses on detection and response.
Is EDR necessary for small businesses?
It depends on risk level; many SMBs benefit from it.
How is EDR priced?
Usually per endpoint subscription.
What is threat hunting?
Proactively searching for hidden threats in systems.
Can EDR stop ransomware?
Yes, through detection and automated response.
How complex is deployment?
Varies from simple to complex depending on tool.
Can EDR integrate with SIEM?
Yes, most tools support SIEM integrations.
What are common mistakes?
Ignoring alerts, poor configuration, lack of training.
Is cloud-based EDR better?
Cloud EDR offers scalability and centralized management.
Conclusion
Endpoint Detection & Response (EDR) solutions are essential for organizations that need deep visibility into endpoint activity and the ability to respond quickly to evolving cyber threats. While tools like CrowdStrike and Microsoft Defender offer enterprise-grade capabilities with strong automation and analytics, options like Sophos, Bitdefender, and ESET provide a more accessible balance of usability and protection for smaller teams. The right choice ultimately depends on your security maturity, team expertise, and existing infrastructure. Rather than chasing a single “best” tool, organizations should focus on aligning EDR capabilities with their risk profile, testing integrations with current systems, and evaluating real-world performance through pilot deployments before making a long-term investment.