Introduction
Zero Trust Network Access (ZTNA) is a modern security framework that restricts access to applications and systems based on strict identity verification and contextual policies. Instead of trusting users or devices inside a network, ZTNA continuously validates every access request—ensuring that only authorized users can connect to specific resources.
Traditional VPN-based access models are no longer sufficient for distributed workforces and cloud-based environments. ZTNA replaces this approach by providing secure, application-level access without exposing the entire network. It minimizes attack surfaces, reduces lateral movement, and enhances security posture.
Common use cases include:
- Secure remote access for employees and contractors
- Replacing legacy VPN solutions
- Protecting internal applications and services
- Enforcing least-privilege access policies
- Securing hybrid and multi-cloud environments
Key evaluation criteria for buyers:
- Identity and access control capabilities
- Integration with identity providers
- Application-level segmentation
- Scalability for remote users
- Performance and latency impact
- Deployment flexibility (cloud or hybrid)
- Integration with security tools
- Policy enforcement and automation
- User experience and ease of access
Best for: Enterprises, security teams, IT administrators, and organizations with remote or hybrid workforces.
Not ideal for: Small teams with simple network setups or those relying on basic security controls.
Key Trends in Zero Trust Network Access (ZTNA)
- Rapid adoption of zero-trust security architectures
- Integration with Secure Access Service Edge (SASE) platforms
- Identity-first security models replacing network-based controls
- AI-driven risk analysis and adaptive access policies
- Increased focus on device posture and compliance checks
- API-based integrations with cloud and SaaS platforms
- Expansion into hybrid and multi-cloud environments
- Continuous authentication and session monitoring
- Convergence with CASB and SWG solutions
- Cloud-native ZTNA deployment models
How We Selected These Tools (Methodology)
- Evaluated market adoption and industry leadership
- Assessed identity-based access control capabilities
- Reviewed scalability and performance for distributed environments
- Considered integration with identity providers and cloud platforms
- Analyzed security features such as segmentation and monitoring
- Included tools suitable for SMBs and enterprises
- Evaluated ease of deployment and usability
- Reviewed support and documentation quality
- Balanced cloud-native and hybrid solutions
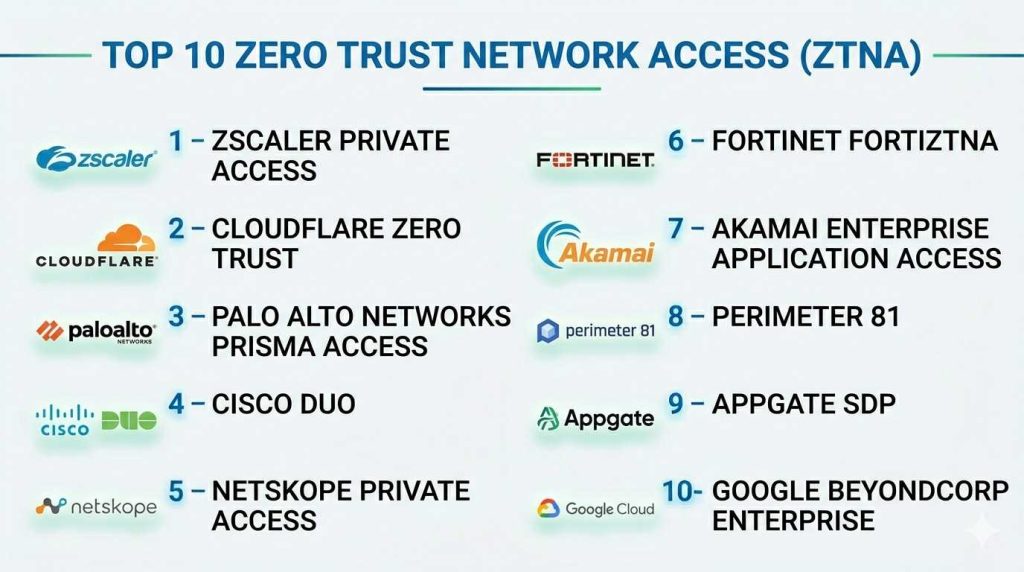
Top Zero Trust Network Access (ZTNA)
#1 — Zscaler Private Access
Short description: Cloud-native ZTNA platform providing secure application access without exposing the network.
Key Features
- Application-level access control
- Identity-based authentication
- Zero-trust architecture
- Continuous monitoring
- Policy enforcement
- Cloud-native deployment
Pros
- Strong scalability
- Excellent security model
Cons
- Premium pricing
- Complex configuration
Platforms / Deployment
Cloud
Security & Compliance
SSO, MFA, RBAC, encryption, audit logs.
Integrations & Ecosystem
Integrates with identity and cloud platforms.
- Azure AD
- Okta
- APIs
- Security tools
Support & Community
Enterprise-grade support.
#2 — Cloudflare Zero Trust
Short description: Integrated ZTNA solution offering secure access and performance optimization.
Key Features
- Secure application access
- Identity integration
- Device posture checks
- Traffic filtering
- Zero-trust policies
Pros
- Easy deployment
- Strong performance
Cons
- Limited advanced features
- Dependency on ecosystem
Platforms / Deployment
Cloud
Security & Compliance
SSO, MFA.
Integrations & Ecosystem
- Identity providers
- APIs
- Cloud platforms
Support & Community
Growing community and support.
#3 — Palo Alto Networks Prisma Access
Short description: Enterprise ZTNA solution integrated into a broader cloud security platform.
Key Features
- Secure access
- Threat prevention
- Application segmentation
- Policy enforcement
- Cloud firewall
Pros
- Strong security features
- Integrated platform
Cons
- Complexity
- Cost
Platforms / Deployment
Cloud
Security & Compliance
SSO, MFA, RBAC.
Integrations & Ecosystem
- Security tools
- Cloud platforms
- APIs
Support & Community
Enterprise-level support.
#4 — Cisco Duo
Short description: Identity-focused ZTNA solution providing secure access and multi-factor authentication.
Key Features
- MFA authentication
- Device trust
- Access control
- Application protection
- User verification
Pros
- Easy to use
- Strong identity security
Cons
- Limited network-level features
- Basic compared to full ZTNA
Platforms / Deployment
Cloud
Security & Compliance
SSO, MFA.
Integrations & Ecosystem
- Identity providers
- APIs
- Security tools
Support & Community
Strong support and documentation.
#5 — Netskope Private Access
Short description: ZTNA solution providing secure application access with strong data protection.
Key Features
- Application access control
- Data protection
- User monitoring
- Policy enforcement
- Cloud-native architecture
Pros
- Strong cloud integration
- Good analytics
Cons
- Pricing
- Learning curve
Platforms / Deployment
Cloud
Security & Compliance
SSO, MFA, encryption.
Integrations & Ecosystem
- SaaS apps
- APIs
- Identity tools
Support & Community
Enterprise support.
#6 — Fortinet FortiZTNA
Short description: ZTNA solution integrated with Fortinet’s security ecosystem.
Key Features
- Application segmentation
- Identity verification
- Threat detection
- Policy enforcement
- Network integration
Pros
- Strong ecosystem integration
- Flexible deployment
Cons
- Complexity
- Requires Fortinet stack
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
SSO, MFA, RBAC.
Integrations & Ecosystem
- Fortinet tools
- APIs
- Security platforms
Support & Community
Reliable enterprise support.
#7 — Akamai Enterprise Application Access
Short description: ZTNA solution focused on secure access to enterprise applications.
Key Features
- Secure application access
- Identity integration
- Policy enforcement
- Threat protection
- Traffic optimization
Pros
- Strong performance
- Global infrastructure
Cons
- Cost
- Complexity
Platforms / Deployment
Cloud
Security & Compliance
SSO, MFA.
Integrations & Ecosystem
- Identity providers
- APIs
- Cloud tools
Support & Community
Enterprise-grade support.
#8 — Perimeter 81
Short description: SMB-friendly ZTNA platform offering secure remote access and network protection.
Key Features
- Secure access
- Network segmentation
- Policy enforcement
- Cloud management
- Monitoring
Pros
- Easy to use
- Affordable
Cons
- Limited enterprise features
- Smaller ecosystem
Platforms / Deployment
Cloud
Security & Compliance
SSO, MFA.
Integrations & Ecosystem
- Cloud tools
- APIs
Support & Community
Good SMB support.
#9 — Appgate SDP
Short description: Software-defined perimeter solution providing zero-trust access control.
Key Features
- Identity-based access
- Micro-segmentation
- Policy enforcement
- Continuous monitoring
- Risk analysis
Pros
- Strong segmentation
- Flexible deployment
Cons
- Complexity
- Learning curve
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
SSO, MFA, RBAC.
Integrations & Ecosystem
- APIs
- Security tools
- Cloud platforms
Support & Community
Enterprise support.
#10 — Google BeyondCorp Enterprise
Short description: Google’s ZTNA solution offering secure access based on zero-trust principles.
Key Features
- Identity-based access
- Device trust checks
- Continuous monitoring
- Policy enforcement
- Cloud-native security
Pros
- Strong Google integration
- Zero-trust maturity
Cons
- Limited outside Google ecosystem
- Complexity
Platforms / Deployment
Cloud
Security & Compliance
SSO, MFA.
Integrations & Ecosystem
- Google Cloud
- APIs
- Identity tools
Support & Community
Strong documentation and support.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Zscaler Private Access | Enterprise | Web | Cloud | Zero-trust access | N/A |
| Cloudflare Zero Trust | Performance | Web | Cloud | Fast deployment | N/A |
| Palo Alto Prisma Access | Enterprise | Web | Cloud | Integrated security | N/A |
| Cisco Duo | Identity security | Web | Cloud | MFA-based access | N/A |
| Netskope Private Access | Data protection | Web | Cloud | Analytics | N/A |
| Fortinet FortiZTNA | Hybrid environments | Web | Cloud/Hybrid | Ecosystem integration | N/A |
| Akamai Enterprise Application Access | Global access | Web | Cloud | Performance | N/A |
| Perimeter 81 | SMB | Web | Cloud | Ease of use | N/A |
| Appgate SDP | Segmentation | Web | Cloud/Hybrid | Micro-segmentation | N/A |
| Google BeyondCorp Enterprise | Google users | Web | Cloud | Zero-trust model | N/A |
Zero Trust Network Access (ZTNA)
| Tool Name | Core | Ease | Integrations | Security | Performance | Support | Value | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Zscaler Private Access | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.5 |
| Cloudflare Zero Trust | 8 | 9 | 8 | 8 | 9 | 8 | 8 | 8.3 |
| Palo Alto Prisma Access | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.5 |
| Cisco Duo | 8 | 9 | 7 | 8 | 8 | 9 | 8 | 8.2 |
| Netskope Private Access | 9 | 8 | 8 | 9 | 8 | 8 | 7 | 8.3 |
| Fortinet FortiZTNA | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 8.0 |
| Akamai Enterprise Application Access | 8 | 7 | 8 | 8 | 9 | 8 | 7 | 8.0 |
| Perimeter 81 | 7 | 9 | 7 | 7 | 8 | 7 | 9 | 7.8 |
| Appgate SDP | 9 | 7 | 8 | 9 | 8 | 8 | 7 | 8.2 |
| Google BeyondCorp Enterprise | 9 | 7 | 8 | 9 | 9 | 8 | 7 | 8.3 |
How to interpret scores:
These scores are comparative and help evaluate tools across key criteria. Higher scores indicate a better balance of features, usability, and value, while lower scores reflect trade-offs such as complexity or limited features.
Which Service Mesh Platforms Is Right for You?
Solo / Freelancer
Basic secure access tools or identity-based solutions are sufficient.
SMB
Perimeter 81 and Cloudflare Zero Trust offer simplicity and affordability.
Mid-Market
Cisco Duo and Netskope provide strong balance and usability.
Enterprise
Zscaler, Palo Alto, and Google BeyondCorp are ideal for large-scale deployments.
Budget vs Premium
Budget tools provide basic access control, while premium tools offer advanced security.
Feature Depth vs Ease of Use
Cloudflare is easier, while Zscaler offers deeper features.
Integrations & Scalability
Enterprise tools provide better scalability and integrations.
Security & Compliance Needs
Highly regulated industries should prioritize advanced ZTNA platforms.
Zero Trust Network Access (ZTNA)
What is ZTNA?
ZTNA is a security model that verifies every access request before granting access.
How is ZTNA different from VPN?
ZTNA provides application-level access, while VPN exposes the entire network.
Is ZTNA cloud-based?
Most modern solutions are cloud-native.
Does ZTNA support remote work?
Yes, it is designed for remote and hybrid environments.
Can ZTNA integrate with identity providers?
Yes, integration with IAM systems is common.
Is ZTNA secure?
Yes, it follows zero-trust principles for strong security.
Does ZTNA improve performance?
It can reduce latency compared to VPNs.
Is ZTNA expensive?
Pricing varies based on features and scale.
What are common mistakes?
Poor policy configuration and lack of monitoring.
Are there alternatives?
SASE platforms combine ZTNA with other security solutions.
Conclusion
Zero Trust Network Access solutions are transforming how organizations secure access to applications and systems by eliminating implicit trust and enforcing strict identity-based controls. As remote work and cloud adoption continue to grow, ZTNA provides a more secure and scalable alternative to traditional VPNs. Enterprise platforms like Zscaler and Palo Alto offer advanced capabilities and deep integrations, while solutions like Cloudflare and Perimeter 81 provide simplicity and faster deployment for smaller teams. The right choice depends on your organization’s size, infrastructure, and security requirements. Start by identifying your access control needs, shortlist a few tools, and conduct pilot testing to ensure seamless integration and optimal performance.