Introduction
Software Composition Analysis (SCA) Tools are solutions that help organizations identify, manage, and secure open-source components used within their applications. In simple terms, they scan your codebase to detect third-party libraries, highlight known vulnerabilities, track licenses, and ensure compliance.
Modern applications rely heavily on open-source dependencies, which can introduce security risks and licensing challenges. SCA tools have become essential for maintaining software supply chain security, especially as regulations and security expectations continue to rise.
Common use cases include:
- Detecting vulnerabilities in open-source dependencies
- Managing software licenses and compliance risks
- Monitoring dependency updates and risks
- Securing software supply chains
- Integrating security checks into CI/CD pipelines
Key evaluation criteria:
- Vulnerability detection accuracy and database coverage
- License compliance and policy enforcement
- Integration with CI/CD and DevOps tools
- Real-time monitoring and alerts
- Support for multiple programming languages
- Ease of use and onboarding
- Reporting and analytics
- Scalability for large projects
- Security features and compliance support
- Cost and licensing model
Best for: Security teams, DevSecOps engineers, developers, and organizations that rely on open-source software in production environments.
Not ideal for: Small projects with minimal dependencies or teams that do not require strict security or compliance controls.
Key Trends in Software Composition Analysis (SCA) Tools
- Shift-left security: Integrating SCA early in the development lifecycle
- AI-driven vulnerability prioritization: Reducing alert fatigue with smarter insights
- Software supply chain security focus: Increased attention due to rising attacks
- Real-time dependency monitoring: Continuous risk detection post-deployment
- SBOM (Software Bill of Materials): Growing adoption for transparency and compliance
- Integration with DevSecOps pipelines: Seamless security checks in CI/CD
- Automated remediation suggestions: Fix recommendations for vulnerabilities
- Multi-language and ecosystem support: Covering modern tech stacks
- Regulatory compliance support: Addressing global standards and requirements
- Cloud-native deployment models: Scalable SaaS solutions
How We Selected These Tools (Methodology)
We evaluated SCA tools based on:
- Market adoption and industry reputation
- Depth and accuracy of vulnerability databases
- License compliance capabilities
- Integration with development and security workflows
- Ease of use and developer experience
- Scalability and performance
- Security and compliance features
- Reporting and analytics capabilities
- Community and vendor support
- Overall value for cost
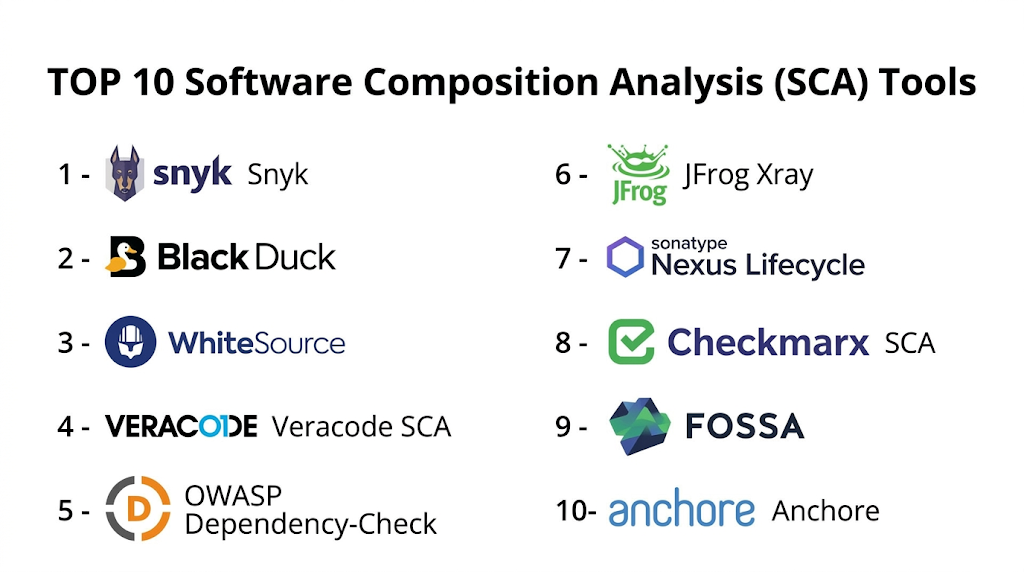
Top 10 Software Composition Analysis (SCA) Tools
#1 — Snyk
Short description: A developer-first security platform that focuses on identifying and fixing vulnerabilities in open-source dependencies.
Key Features
- Open-source vulnerability scanning
- Real-time monitoring
- Automated fix suggestions
- Integration with CI/CD pipelines
- License compliance checks
- Developer-friendly interface
Pros
- Easy to integrate into workflows
- Strong developer experience
Cons
- Pricing can scale quickly
- Advanced features require paid plans
Platforms / Deployment
Cloud
Security & Compliance
SSO, RBAC, encryption
Integrations & Ecosystem
Snyk integrates deeply with modern DevOps tools, making it easy to embed security into development workflows.
- GitHub
- GitLab
- Bitbucket
- CI/CD pipelines
Support & Community
Strong community and vendor support.
#2 — Black Duck (by Synopsys)
Short description: An enterprise-grade SCA solution focused on open-source security and license compliance.
Key Features
- Comprehensive vulnerability database
- License compliance management
- Risk analysis and reporting
- Policy enforcement
- SBOM generation
Pros
- Strong compliance capabilities
- Enterprise-ready
Cons
- Complex setup
- Expensive
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
RBAC, encryption, audit logs
Integrations & Ecosystem
Black Duck integrates with enterprise development environments and security tools.
- CI/CD tools
- SCM systems
- DevOps platforms
Support & Community
Enterprise-level support.
#3 — WhiteSource (now Mend)
Short description: A widely used SCA tool providing vulnerability management and license compliance for open-source components.
Key Features
- Open-source scanning
- License compliance tracking
- Automated remediation
- Real-time alerts
- Policy management
Pros
- Strong automation features
- Good integration capabilities
Cons
- UI can be complex
- Pricing varies
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
RBAC, encryption
Integrations & Ecosystem
Mend integrates with a wide range of DevOps tools and environments.
- Git platforms
- CI/CD pipelines
- Issue trackers
Support & Community
Strong vendor support.
#4 — Veracode SCA
Short description: A cloud-based SCA solution integrated into Veracode’s application security platform.
Key Features
- Dependency scanning
- Vulnerability management
- Policy enforcement
- Risk prioritization
- Developer guidance
Pros
- Integrated security platform
- Strong reporting
Cons
- Expensive
- Limited customization
Platforms / Deployment
Cloud
Security & Compliance
SSO, encryption, audit logs
Integrations & Ecosystem
Veracode integrates with development and security workflows.
- CI/CD tools
- SCM platforms
Support & Community
Enterprise support.
#5 — OWASP Dependency-Check
Short description: An open-source tool that identifies vulnerabilities in project dependencies.
Key Features
- Dependency scanning
- Vulnerability database integration
- Report generation
- CI/CD integration
- Open-source
Pros
- Free to use
- Simple setup
Cons
- Limited advanced features
- Requires manual configuration
Platforms / Deployment
Self-hosted
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Works with development pipelines and tools.
- CI/CD tools
- Build systems
Support & Community
Active open-source community.
#6 — JFrog Xray
Short description: A security and compliance tool integrated with JFrog’s artifact management platform.
Key Features
- Deep artifact scanning
- Vulnerability detection
- License compliance
- Continuous monitoring
- Policy enforcement
Pros
- Strong integration with artifact repositories
- Real-time scanning
Cons
- Requires JFrog ecosystem
- Complex setup
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
RBAC, encryption
Integrations & Ecosystem
Works within JFrog ecosystem and DevOps pipelines.
- Artifactory
- CI/CD tools
Support & Community
Strong enterprise support.
#7 — Sonatype Nexus Lifecycle
Short description: A policy-based SCA tool focused on managing open-source risk and compliance.
Key Features
- Policy enforcement
- Vulnerability detection
- License compliance
- Continuous monitoring
- Reporting and analytics
Pros
- Strong policy management
- Good reporting
Cons
- Learning curve
- Pricing can be high
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
RBAC, audit logs
Integrations & Ecosystem
Integrates with development and DevOps tools.
- Nexus Repository
- CI/CD pipelines
Support & Community
Enterprise support.
#8 — Checkmarx SCA
Short description: A component of Checkmarx’s application security platform focusing on open-source risk.
Key Features
- Dependency scanning
- Vulnerability management
- License compliance
- Integration with security tools
- Risk prioritization
Pros
- Strong security integration
- Enterprise-ready
Cons
- Complex setup
- Costly
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
RBAC, encryption
Integrations & Ecosystem
Works with DevSecOps pipelines.
- SCM tools
- CI/CD platforms
Support & Community
Enterprise support.
#9 — FOSSA
Short description: A developer-friendly SCA tool focused on license compliance and vulnerability management.
Key Features
- License compliance tracking
- Vulnerability detection
- Automated policy enforcement
- Reporting tools
- CI/CD integration
Pros
- Easy to use
- Strong compliance features
Cons
- Limited advanced security features
- Pricing varies
Platforms / Deployment
Cloud
Security & Compliance
SSO, RBAC
Integrations & Ecosystem
FOSSA integrates with modern development workflows.
- Git platforms
- CI/CD tools
Support & Community
Good vendor support.
#10 — Anchore
Short description: A security tool focused on container and dependency scanning.
Key Features
- Container image scanning
- Vulnerability detection
- Policy enforcement
- CI/CD integration
- Open-source options
Pros
- Strong container security
- Flexible deployment
Cons
- Focused on containers
- Requires setup
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
RBAC, policy controls
Integrations & Ecosystem
Works with container ecosystems and DevOps pipelines.
- Docker
- Kubernetes
- CI/CD tools
Support & Community
Active community.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Snyk | Developer-first | Web | Cloud | Fix suggestions | N/A |
| Black Duck | Enterprise | Cross-platform | Hybrid | Compliance | N/A |
| Mend | Automation | Cross-platform | Hybrid | Remediation | N/A |
| Veracode | Security platform | Web | Cloud | Risk analysis | N/A |
| OWASP DC | Open-source | Cross-platform | Self-hosted | Free scanning | N/A |
| JFrog Xray | Artifacts | Cross-platform | Hybrid | Artifact scanning | N/A |
| Sonatype | Policy control | Cross-platform | Hybrid | Governance | N/A |
| Checkmarx | Enterprise | Cross-platform | Hybrid | Security integration | N/A |
| FOSSA | Compliance | Web | Cloud | License tracking | N/A |
| Anchore | Containers | Cross-platform | Hybrid | Image scanning | N/A |
Software Composition Analysis (SCA) Tools Scoring
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Snyk | 9 | 9 | 10 | 9 | 9 | 9 | 8 | 9.1 |
| Black Duck | 9 | 7 | 9 | 10 | 9 | 9 | 6 | 8.6 |
| Mend | 9 | 8 | 9 | 9 | 9 | 9 | 7 | 8.7 |
| Veracode | 8 | 8 | 9 | 9 | 8 | 9 | 7 | 8.3 |
| OWASP DC | 7 | 7 | 7 | 7 | 7 | 8 | 10 | 7.6 |
| JFrog Xray | 9 | 7 | 9 | 9 | 9 | 9 | 7 | 8.5 |
| Sonatype | 9 | 7 | 9 | 9 | 9 | 9 | 7 | 8.5 |
| Checkmarx | 8 | 7 | 8 | 9 | 8 | 9 | 7 | 8.1 |
| FOSSA | 8 | 8 | 8 | 8 | 8 | 8 | 8 | 8.0 |
| Anchore | 8 | 7 | 8 | 8 | 8 | 8 | 8 | 8.0 |
How to interpret scores:
- Scores reflect comparative strengths across tools
- Enterprise tools score higher in compliance and security
- Developer-focused tools score higher in ease of use
- Open-source tools provide high value
- Choose based on security maturity and workflow needs
Which Software Composition Analysis (SCA) Tools Is Right for You?
Solo / Freelancer
- Use OWASP Dependency-Check or Snyk (free tier)
- Focus on simplicity and cost
SMB
- Snyk or FOSSA
- Balance ease of use and functionality
Mid-Market
- Mend or Sonatype Nexus Lifecycle
- Focus on automation and policy enforcement
Enterprise
- Black Duck or JFrog Xray
- Focus on compliance and scalability
Budget vs Premium
- Open-source tools provide strong value
- Enterprise tools offer advanced compliance
Feature Depth vs Ease of Use
- Black Duck = powerful
- Snyk = user-friendly
Integrations & Scalability
- Choose tools with strong CI/CD integration
- Ensure multi-language support
Security & Compliance Needs
- Enterprises should prioritize audit logs and policy enforcement
- Smaller teams can focus on vulnerability scanning
Frequently Asked Questions (FAQs)
What is SCA?
SCA identifies and manages open-source components in applications.
Why is SCA important?
It helps detect vulnerabilities and manage license risks.
Are SCA tools free?
Some are open-source; others are commercial.
What is SBOM?
A Software Bill of Materials listing all components in an application.
Can SCA tools fix vulnerabilities?
Some provide automated fix suggestions.
Do SCA tools integrate with CI/CD?
Yes, most modern tools support CI/CD integration.
Are SCA tools necessary for small teams?
Depends on security and compliance needs.
What languages do SCA tools support?
Most support multiple programming languages.
Can SCA tools monitor production apps?
Yes, many offer continuous monitoring.
Can I switch tools later?
Yes, but configurations may need adjustment.
Conclusion
Software Composition Analysis (SCA) Tools are critical for securing modern applications and managing open-source risks. They help organizations detect vulnerabilities early, ensure compliance, and maintain a secure software supply chain.