Introduction
Service Mesh Platforms are infrastructure layers designed to manage service-to-service communication in microservices architectures. In simple terms, they help applications made up of many small services talk to each other securely, reliably, and efficiently—without requiring developers to write complex networking code.
As organizations increasingly adopt Kubernetes and cloud-native architectures, service meshes have become essential. They provide visibility, traffic control, and security across distributed systems, which are often difficult to manage at scale.
Common use cases include:
- Managing microservices communication in Kubernetes environments
- Enforcing zero-trust security between services
- Observability (metrics, logs, tracing) across distributed systems
- Traffic routing (canary deployments, A/B testing)
- Resilience (retries, circuit breaking, failover)
Key evaluation criteria:
- Ease of deployment and management
- Performance overhead (latency impact)
- Security features (mTLS, RBAC, encryption)
- Observability and monitoring capabilities
- Integration with Kubernetes and cloud platforms
- Ecosystem and community support
- Multi-cluster and multi-cloud support
- Automation and policy management
Best for: DevOps teams, platform engineers, SREs, and enterprises managing microservices at scale—especially those using Kubernetes.
Not ideal for: Small applications, monolithic systems, or teams without Kubernetes expertise. In such cases, simpler API gateways or load balancers may be more practical.
Key Trends in Service Mesh Platforms
- AI-driven observability: Platforms are incorporating AI to detect anomalies, predict failures, and optimize traffic routing.
- Sidecar-less architectures: Emerging models reduce reliance on sidecars to improve performance and simplify operations.
- Zero-trust security by default: mTLS and identity-based access control are becoming baseline requirements.
- Multi-cluster and multi-cloud support: Organizations demand seamless communication across regions and cloud providers.
- GitOps and automation integration: Declarative configurations and CI/CD pipelines are now standard.
- eBPF-based networking: Reduces overhead and improves observability without sidecars.
- Platform engineering alignment: Service meshes are becoming part of internal developer platforms (IDPs).
- Cost optimization features: Better traffic control and resource management to reduce cloud costs.
- Improved developer experience: Simplified dashboards, abstractions, and APIs.
- Standardization (e.g., OpenTelemetry): Unified observability frameworks gaining traction.
How We Selected These Tools (Methodology)
We evaluated Service Mesh Platforms based on the following criteria:
- Strong adoption in Kubernetes and cloud-native ecosystems
- Feature completeness (traffic control, security, observability)
- Proven reliability and performance at scale
- Security capabilities such as mTLS, RBAC, and policy enforcement
- Integration with major cloud providers and DevOps tools
- Active community or vendor-backed support
- Flexibility across deployment models (cloud, hybrid, on-prem)
- Ease of onboarding and operational complexity
- Suitability for different organization sizes (SMB to enterprise)
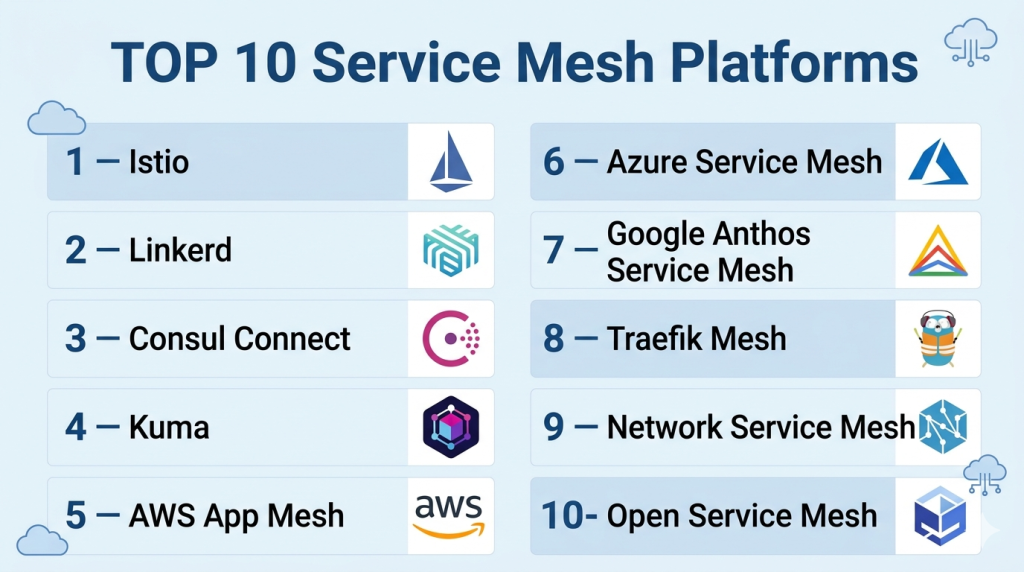
Top 10 Service Mesh Platforms
#1 — Istio
Short description: A widely adopted open-source service mesh offering advanced traffic management, security, and observability for Kubernetes environments.
Key Features
- Advanced traffic routing and load balancing
- Mutual TLS (mTLS) encryption by default
- Rich observability with metrics, logs, tracing
- Policy enforcement and access control
- Multi-cluster and multi-cloud support
- Integration with Envoy proxy
Pros
- Highly feature-rich and flexible
- Strong community and ecosystem
Cons
- Complex to deploy and manage
- Higher resource overhead
Platforms / Deployment
Cloud / Self-hosted / Hybrid
Security & Compliance
mTLS, RBAC, encryption, audit logs
Integrations & Ecosystem
Istio integrates deeply with Kubernetes and supports tools like Prometheus, Grafana, and Jaeger. It also works with CI/CD pipelines and cloud providers.
- Kubernetes
- Prometheus
- Grafana
- Jaeger
- Envoy
Support & Community
Large open-source community, extensive documentation, and enterprise support via vendors.
#2 — Linkerd
Short description: A lightweight, developer-friendly service mesh focused on simplicity and performance.
Key Features
- Automatic mTLS
- Low-latency proxy
- Simple installation and operation
- Built-in observability dashboard
- Kubernetes-native design
Pros
- Easy to use and deploy
- Minimal performance overhead
Cons
- Fewer advanced features than Istio
- Limited customization
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
mTLS, encryption
Integrations & Ecosystem
Works seamlessly with Kubernetes and monitoring tools.
- Kubernetes
- Prometheus
- Grafana
Support & Community
Active open-source community, good documentation.
#3 — Consul Connect (HashiCorp Consul)
Short description: A service mesh solution integrated with service discovery and configuration management.
Key Features
- Service discovery and segmentation
- mTLS encryption
- Multi-datacenter support
- Intent-based security policies
- Integration with HashiCorp ecosystem
Pros
- Strong multi-cloud support
- Unified service networking solution
Cons
- Requires understanding of Consul ecosystem
- Operational complexity at scale
Platforms / Deployment
Cloud / Self-hosted / Hybrid
Security & Compliance
mTLS, ACLs, encryption
Integrations & Ecosystem
Deep integration with Terraform and Vault.
- Terraform
- Vault
- Kubernetes
- Nomad
Support & Community
Enterprise support available; strong community.
#4 — Kuma
Short description: A modern service mesh by Kong designed for multi-zone deployments and ease of use.
Key Features
- Universal (Kubernetes + VMs) support
- Built-in mTLS
- Multi-zone architecture
- Policy-driven traffic control
- Envoy-based
Pros
- Simple architecture
- Multi-environment support
Cons
- Smaller ecosystem
- Fewer advanced features
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
mTLS, RBAC
Integrations & Ecosystem
Works with Kong ecosystem and observability tools.
- Kubernetes
- Prometheus
- Grafana
Support & Community
Moderate community; vendor support via Kong.
#5 — AWS App Mesh
Short description: A managed service mesh by AWS for applications running on AWS infrastructure.
Key Features
- Fully managed service mesh
- Integration with AWS services
- Traffic routing and observability
- mTLS support
- Envoy-based
Pros
- Easy integration with AWS
- Managed infrastructure
Cons
- Vendor lock-in
- Limited outside AWS
Platforms / Deployment
Cloud
Security & Compliance
mTLS, IAM integration
Integrations & Ecosystem
Native AWS integrations.
- ECS
- EKS
- CloudWatch
- X-Ray
Support & Community
Enterprise-grade AWS support.
#6 — Azure Service Mesh (Open Service Mesh / AKS integrations)
Short description: Microsoft’s service mesh approach integrated into Azure Kubernetes environments.
Key Features
- Lightweight mesh
- Native AKS integration
- Traffic splitting
- Observability tools
- Security policies
Pros
- Seamless Azure integration
- Easy setup in AKS
Cons
- Limited flexibility outside Azure
- Fewer advanced features
Platforms / Deployment
Cloud
Security & Compliance
mTLS, Azure security integration
Integrations & Ecosystem
Works with Azure ecosystem.
- AKS
- Azure Monitor
- Application Insights
Support & Community
Backed by Microsoft; moderate community.
#7 — Google Anthos Service Mesh
Short description: A managed service mesh based on Istio for Google Cloud and hybrid environments.
Key Features
- Managed Istio experience
- Multi-cluster support
- Advanced observability
- Security policies
- Traffic management
Pros
- Enterprise-grade reliability
- Strong multi-cloud capabilities
Cons
- Complex pricing
- Google Cloud dependency
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
mTLS, IAM integration
Integrations & Ecosystem
Deep integration with Google Cloud services.
- GKE
- Cloud Monitoring
- Cloud Logging
Support & Community
Enterprise support via Google.
#8 — Traefik Mesh
Short description: A simple service mesh built on top of Traefik proxy for Kubernetes environments.
Key Features
- Lightweight deployment
- Kubernetes-native
- Simple configuration
- Basic observability
- Traffic routing
Pros
- Easy to set up
- Low overhead
Cons
- Limited enterprise features
- Smaller ecosystem
Platforms / Deployment
Self-hosted
Security & Compliance
Basic encryption, Not publicly stated
Integrations & Ecosystem
Works with Traefik and Kubernetes.
- Kubernetes
- Traefik Proxy
Support & Community
Smaller but active community.
#9 — Network Service Mesh (NSM)
Short description: A Kubernetes-native project focused on advanced networking use cases.
Key Features
- Layer 2–7 networking
- Service chaining
- High-performance networking
- Kubernetes-native APIs
- Extensible architecture
Pros
- Advanced networking capabilities
- Flexible architecture
Cons
- Steeper learning curve
- Less mainstream adoption
Platforms / Deployment
Self-hosted
Security & Compliance
Not publicly stated
Integrations & Ecosystem
Focused on Kubernetes networking.
- Kubernetes
- CNI plugins
Support & Community
Niche but growing community.
#10 — Open Service Mesh (OSM)
Short description: A lightweight, CNCF-hosted service mesh focused on simplicity and Kubernetes integration.
Key Features
- Simple configuration
- mTLS support
- Traffic shaping
- Observability
- Kubernetes-native
Pros
- Easy to deploy
- Lightweight
Cons
- Limited advanced features
- Smaller ecosystem
Platforms / Deployment
Self-hosted
Security & Compliance
mTLS, encryption
Integrations & Ecosystem
Works with standard Kubernetes tools.
- Kubernetes
- Prometheus
- Grafana
Support & Community
Moderate community support.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Istio | Enterprises | Kubernetes | Hybrid | Advanced traffic control | N/A |
| Linkerd | SMBs | Kubernetes | Cloud/Self-hosted | Simplicity | N/A |
| Consul Connect | Multi-cloud | Kubernetes/VMs | Hybrid | Service discovery | N/A |
| Kuma | Multi-zone | Kubernetes/VMs | Cloud/Self-hosted | Multi-zone support | N/A |
| AWS App Mesh | AWS users | AWS | Cloud | Managed service | N/A |
| Azure Service Mesh | Azure users | AKS | Cloud | Native integration | N/A |
| Anthos Service Mesh | Enterprises | GKE | Hybrid | Managed Istio | N/A |
| Traefik Mesh | Small teams | Kubernetes | Self-hosted | Lightweight | N/A |
| NSM | Advanced networking | Kubernetes | Self-hosted | Layer 2–7 networking | N/A |
| OSM | Simplicity | Kubernetes | Self-hosted | Lightweight | N/A |
Service Mesh Platforms Scoring
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Istio | 9 | 6 | 9 | 9 | 8 | 9 | 7 | 8.2 |
| Linkerd | 7 | 9 | 7 | 8 | 9 | 8 | 8 | 8.1 |
| Consul | 8 | 6 | 9 | 9 | 8 | 8 | 7 | 8.0 |
| Kuma | 7 | 7 | 7 | 8 | 8 | 7 | 7 | 7.4 |
| AWS App Mesh | 8 | 8 | 9 | 9 | 8 | 9 | 7 | 8.3 |
| Azure Mesh | 7 | 8 | 8 | 8 | 8 | 8 | 7 | 7.8 |
| Anthos | 9 | 7 | 9 | 9 | 9 | 9 | 6 | 8.5 |
| Traefik | 6 | 9 | 6 | 6 | 8 | 7 | 8 | 7.3 |
| NSM | 8 | 5 | 7 | 7 | 9 | 6 | 7 | 7.2 |
| OSM | 6 | 8 | 6 | 7 | 8 | 7 | 8 | 7.3 |
How to interpret scores:
- Scores are relative comparisons, not absolute benchmarks.
- A higher score reflects better balance across enterprise needs.
- Simpler tools may score lower on features but higher on ease of use.
- Enterprise tools often trade simplicity for flexibility and control.
- Always validate based on your specific environment and team expertise.
Which Service Mesh Platforms Is Right for You?
Solo / Freelancer
- Not typically needed unless working with Kubernetes labs
- Consider lightweight options like Linkerd or Traefik Mesh
SMB
- Choose Linkerd or OSM for simplicity and low overhead
- Avoid overly complex platforms like Istio
Mid-Market
- Consider Kuma or Consul for balance between features and usability
- Ensure integration with CI/CD and monitoring tools
Enterprise
- Istio or Anthos Service Mesh are strong choices
- AWS or Azure-native meshes if locked into those ecosystems
Budget vs Premium
- Open-source tools (Istio, Linkerd) offer cost efficiency
- Managed services (AWS, Google) reduce operational burden but cost more
Feature Depth vs Ease of Use
- Istio = maximum control
- Linkerd = simplicity and speed
Integrations & Scalability
- Choose tools with strong Kubernetes and cloud integrations
- Multi-cluster support is critical for scaling
Security & Compliance Needs
- Enterprises should prioritize mTLS, RBAC, and audit logs
- Managed meshes often provide better compliance alignment
Frequently Asked Questions (FAQs)
What is a service mesh used for?
A service mesh manages communication between microservices, providing security, observability, and traffic control.
Is a service mesh required for Kubernetes?
Not always, but it becomes essential as microservices scale and complexity increases.
How much do service mesh platforms cost?
Costs vary. Open-source tools are free, while managed services follow usage-based pricing.
Is Istio better than Linkerd?
Istio offers more features, while Linkerd focuses on simplicity and performance.
What is mTLS in service mesh?
Mutual TLS encrypts communication and verifies identity between services.
Are service meshes secure?
Yes, when properly configured with mTLS, RBAC, and policies.
How long does implementation take?
It can range from hours (simple setups) to weeks (enterprise deployments).
Can service meshes work without Kubernetes?
Some can (e.g., Consul), but most are Kubernetes-focused.
What are common mistakes?
Overcomplicating deployments, ignoring observability, and misconfiguring security policies.
Can you switch service mesh platforms?
Yes, but migration can be complex and requires planning.
Conclusion
Service Mesh Platforms have become a foundational component of modern cloud-native architectures. They simplify complex service communication, enhance security, and provide deep observability.