Introduction
Customer Identity and Access Management (CIAM) refers to systems that help businesses securely manage customer identities, authentication, and authorization across digital platforms. Unlike traditional IAM (focused on employees), CIAM is designed for external users—customers, partners, and end users—at scale.
In CIAM is more critical than ever due to rising cybersecurity threats, stricter privacy regulations, and demand for seamless digital experiences. Businesses must balance security with convenience, ensuring users can log in easily while protecting sensitive data.
Common Use Cases
- Secure login and registration for SaaS platforms and apps
- Managing customer profiles and preferences across channels
- Enabling passwordless authentication (OTP, biometrics)
- Supporting social logins (Google, Apple, etc.)
- Ensuring compliance with regulations like GDPR and data privacy laws
What Buyers Should Evaluate
- Authentication methods (MFA, passwordless, social login)
- Scalability (millions of users, global performance)
- Security features (encryption, fraud detection)
- Compliance support (GDPR, SOC 2, etc.)
- Integration ecosystem (APIs, SDKs, third-party tools)
- Customization (branding, user flows)
- Developer experience (documentation, SDKs)
- Pricing model (MAU-based, tiered, enterprise)
- Analytics and user insights
- Deployment flexibility (cloud, hybrid, self-hosted)
Best for: SaaS companies, fintech, e-commerce, healthcare platforms, and enterprises managing large user bases. Ideal for IT managers, developers, and product teams.
Not ideal for: Small projects or internal-only tools where basic authentication (e.g., Firebase Auth or simple OAuth libraries) is sufficient.
Key Trends in Customer IAM (CIAM)
- Passwordless Authentication Growth: OTP, biometrics, and passkeys replacing traditional passwords
- AI-Powered Fraud Detection: Behavioral analytics to detect suspicious login patterns
- Privacy-First Architecture: Built-in compliance with global data protection laws
- Decentralized Identity Models: Early adoption of user-controlled identity frameworks
- Low-Code Identity Workflows: Visual builders for authentication flows
- Omnichannel Identity: Unified identity across web, mobile, IoT, and APIs
- API-First Platforms: Strong developer tooling and extensibility
- Real-Time Risk Scoring: Adaptive authentication based on user behavior
- Multi-Tenant Architectures: Supporting SaaS platforms with multiple customers
- Usage-Based Pricing: MAU-based billing becoming standard
How We Selected These Tools (Methodology)
- Evaluated market adoption and brand recognition
- Assessed feature completeness and innovation
- Reviewed security posture and compliance signals
- Considered developer experience and documentation quality
- Analyzed integration ecosystems and extensibility
- Checked performance and scalability capabilities
- Balanced tools across enterprise, SMB, and developer-first segments
- Factored community support and ecosystem maturity
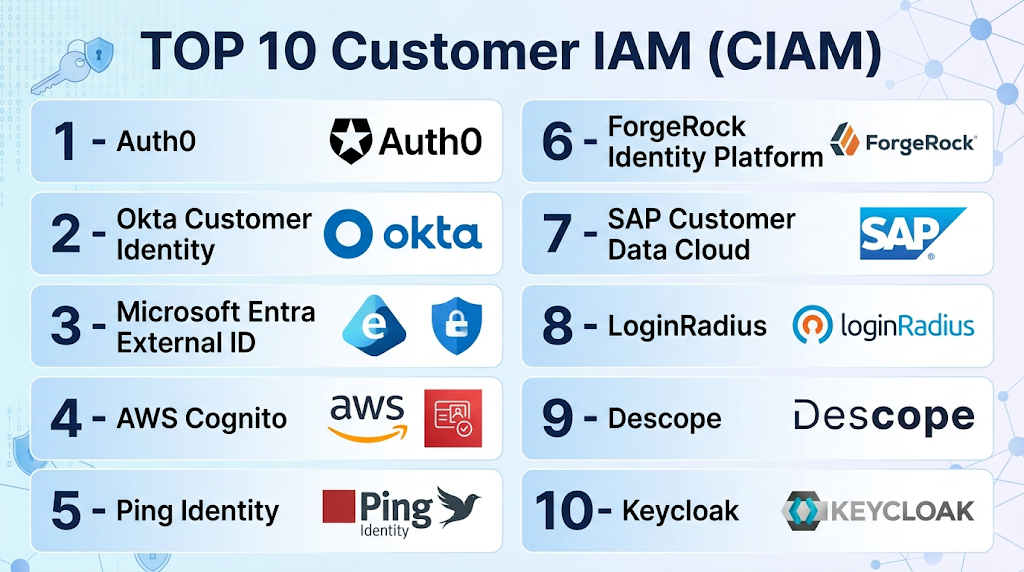
Top Customer IAM (CIAM)
#1 — Auth0 (by Okta)
Short description: A leading CIAM platform offering flexible authentication and identity management for developers and enterprises.
Key Features
- Universal login and SSO
- MFA and passwordless authentication
- Social identity providers
- Custom authentication flows
- API security and token management
- User analytics and monitoring
Pros
- Highly customizable and developer-friendly
- Large integration ecosystem
Cons
- Pricing can become expensive at scale
- Learning curve for advanced features
Platforms / Deployment
Cloud
Security & Compliance
SSO, MFA, RBAC, encryption, audit logs
SOC 2, GDPR support
Integrations & Ecosystem
Strong ecosystem with APIs and SDKs.
- CRM tools
- Analytics platforms
- Cloud providers
- Custom APIs
Support & Community
Extensive documentation and large developer community
#2 — Okta Customer Identity
Short description: Enterprise-grade CIAM solution focused on scalability and security.
Key Features
- Adaptive MFA
- Lifecycle management
- API access control
- Identity federation
- Risk-based authentication
Pros
- Strong enterprise security
- Reliable performance
Cons
- Complex setup
- Higher cost
Platforms / Deployment
Cloud
Security & Compliance
SSO, MFA, audit logs
SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
Wide enterprise integrations
- HR systems
- SaaS apps
- APIs
Support & Community
Enterprise-grade support, strong ecosystem
#3 — Microsoft Entra External ID
Short description: CIAM offering from Microsoft integrated with Azure ecosystem.
Key Features
- Identity federation
- Conditional access
- B2C identity management
- Integration with Azure services
- Custom user journeys
Pros
- Seamless Microsoft integration
- Strong enterprise capabilities
Cons
- Complex configuration
- Requires Azure expertise
Platforms / Deployment
Cloud
Security & Compliance
SSO, MFA, RBAC
Compliance varies
Integrations & Ecosystem
Deep Microsoft ecosystem integration
- Azure services
- Microsoft apps
- APIs
Support & Community
Strong enterprise support
#4 — AWS Cognito
Short description: Developer-focused CIAM tool tightly integrated with AWS services.
Key Features
- User pools and identity pools
- Social login support
- MFA and device tracking
- Token-based authentication
- Serverless integration
Pros
- Cost-effective for AWS users
- Scalable
Cons
- Limited UI customization
- Complex setup
Platforms / Deployment
Cloud
Security & Compliance
MFA, encryption
Compliance varies
Integrations & Ecosystem
AWS-native integrations
- Lambda
- API Gateway
- S3
Support & Community
Strong developer community
#5 — Ping Identity (PingOne for Customers)
Short description: Enterprise CIAM solution with strong identity orchestration.
Key Features
- Identity orchestration
- MFA and adaptive authentication
- API security
- Customer profile management
- Risk-based policies
Pros
- Strong security features
- Flexible workflows
Cons
- Expensive
- Complex deployment
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
SSO, MFA, audit logs
SOC 2, GDPR
Integrations & Ecosystem
Enterprise integrations
- APIs
- Identity providers
- SaaS apps
Support & Community
Enterprise-level support
#6 — ForgeRock Identity Platform
Short description: Comprehensive identity platform for large-scale deployments.
Key Features
- Identity orchestration
- Access management
- User journey customization
- AI-based fraud detection
- API security
Pros
- Highly scalable
- Advanced customization
Cons
- Complex setup
- High cost
Platforms / Deployment
Cloud / Self-hosted
Security & Compliance
SSO, MFA, RBAC
Compliance varies
Integrations & Ecosystem
Extensive APIs and integrations
Support & Community
Strong enterprise support
#7 — SAP Customer Data Cloud
Short description: CIAM solution focused on customer data and consent management.
Key Features
- Consent and preference management
- Identity federation
- Profile management
- Compliance tools
- Customer insights
Pros
- Strong compliance features
- Good for regulated industries
Cons
- Limited flexibility
- Enterprise-focused pricing
Platforms / Deployment
Cloud
Security & Compliance
GDPR-focused features
Integrations & Ecosystem
SAP ecosystem integrations
Support & Community
Enterprise support
#8 — LoginRadius
Short description: Developer-friendly CIAM platform with quick deployment.
Key Features
- Social login
- MFA and SSO
- User management APIs
- Analytics
- Passwordless login
Pros
- Easy to implement
- Good pricing for SMBs
Cons
- Limited advanced customization
- Smaller ecosystem
Platforms / Deployment
Cloud
Security & Compliance
MFA, encryption
Compliance varies
Integrations & Ecosystem
APIs and common integrations
Support & Community
Good documentation
#9 — Descope
Short description: Modern CIAM platform focused on no-code authentication flows.
Key Features
- No-code workflow builder
- Passwordless authentication
- MFA
- API-based integration
- User management
Pros
- Easy to use
- Fast implementation
Cons
- Newer platform
- Limited enterprise features
Platforms / Deployment
Cloud
Security & Compliance
MFA, encryption
Not publicly stated
Integrations & Ecosystem
Growing ecosystem
Support & Community
Emerging community
#10 — Keycloak
Short description: Open-source identity and access management platform.
Key Features
- SSO and identity federation
- MFA
- User management
- Role-based access control
- Custom themes
Pros
- Free and open-source
- Highly customizable
Cons
- Requires maintenance
- Limited official support
Platforms / Deployment
Self-hosted
Security & Compliance
SSO, MFA, RBAC
Compliance varies
Integrations & Ecosystem
APIs and community plugins
Support & Community
Strong open-source community
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Auth0 | Developers & enterprises | Web | Cloud | Custom auth flows | N/A |
| Okta | Enterprise security | Web | Cloud | Adaptive MFA | N/A |
| Microsoft Entra | Azure users | Web | Cloud | Azure integration | N/A |
| AWS Cognito | AWS developers | Web | Cloud | Serverless integration | N/A |
| Ping Identity | Enterprise IAM | Web | Cloud/Hybrid | Identity orchestration | N/A |
| ForgeRock | Large enterprises | Web | Cloud/Self-hosted | AI fraud detection | N/A |
| SAP CDC | Compliance-heavy industries | Web | Cloud | Consent management | N/A |
| LoginRadius | SMBs | Web | Cloud | Easy deployment | N/A |
| Descope | Startups | Web | Cloud | No-code workflows | N/A |
| Keycloak | Open-source users | Web | Self-hosted | Free IAM | N/A |
Customer IAM (CIAM)
Scoring Table
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Auth0 | 9 | 8 | 9 | 9 | 9 | 9 | 7 | 8.7 |
| Okta | 9 | 7 | 9 | 10 | 9 | 9 | 6 | 8.6 |
| Microsoft Entra | 8 | 7 | 9 | 9 | 9 | 8 | 7 | 8.3 |
| AWS Cognito | 8 | 6 | 8 | 8 | 9 | 7 | 8 | 7.8 |
| Ping Identity | 9 | 6 | 8 | 10 | 9 | 8 | 6 | 8.2 |
| ForgeRock | 9 | 5 | 8 | 10 | 9 | 8 | 6 | 8.1 |
| SAP CDC | 8 | 6 | 7 | 9 | 8 | 8 | 6 | 7.7 |
| LoginRadius | 7 | 8 | 7 | 7 | 8 | 7 | 8 | 7.6 |
| Descope | 7 | 9 | 7 | 7 | 7 | 6 | 8 | 7.4 |
| Keycloak | 8 | 5 | 7 | 8 | 7 | 6 | 9 | 7.3 |
How to interpret scores:
- Scores are relative comparisons, not absolute performance metrics
- Higher “Core” and “Security” scores indicate enterprise readiness
- “Ease” matters more for smaller teams and fast deployment
- “Value” reflects pricing flexibility and ROI
- Choose based on your priorities, not just the highest score
Which Service Mesh Platforms Is Right for You?
Solo / Freelancer
- Use Keycloak or Descope
- Focus on low cost and simple setup
SMB
- LoginRadius or Auth0
- Balance ease of use with scalability
Mid-Market
- AWS Cognito or Microsoft Entra
- Strong integrations and flexibility
Enterprise
- Okta, Ping Identity, ForgeRock
- Advanced security and compliance
Budget vs Premium
- Budget: Keycloak, LoginRadius
- Premium: Okta, ForgeRock
Feature Depth vs Ease of Use
- Feature-rich: ForgeRock, Ping
- Easy-to-use: Descope, LoginRadius
Integrations & Scalability
- AWS ecosystem: Cognito
- Microsoft ecosystem: Entra
Security & Compliance Needs
- High compliance: SAP CDC, Okta
- Moderate: LoginRadius, Descope
Customer IAM (CIAM)
What is CIAM?
CIAM manages customer identities and authentication securely at scale.
How is CIAM different from IAM?
CIAM focuses on external users, while IAM is for internal employees.
How is CIAM priced?
Typically based on monthly active users (MAU).
Is CIAM necessary for small apps?
Not always; simple auth tools may suffice.
What is passwordless authentication?
Login without passwords using OTP, biometrics, or passkeys.
Can CIAM handle millions of users?
Yes, most enterprise CIAM tools are designed for scale.
How long does implementation take?
From days (simple) to months (enterprise setups).
What are common mistakes?
Ignoring UX, overcomplicating workflows, poor integration planning.
Can I switch CIAM providers later?
Yes, but migration can be complex.
Are open-source CIAM tools reliable?
Yes, but require maintenance and expertise.
Conclusion
Customer IAM (CIAM) is no longer optional—it’s a core layer of modern digital infrastructure. From improving user experience to ensuring compliance and security, the right CIAM platform can significantly impact business outcomes.